A newer version of this document is available. Customers should click here to go to the newest version.
Profile Targets in the Hyper-V* Environment
Configure your Windows* system to enable hardware event-based performance analysis in the Hyper-V virtualization environment.
VTune Profiler supports performance profiling in the Hyper-V environment with some limitations applicable to the event-based sampling collection. So, before you start the analysis, make sure your system configuration satisfies the requirements.
Verify Your System Configuration for Hardware Analysis
For the hardware analysis in your Hyper-V environment, make sure your system runs on:
Intel microarchitectures code named Skylake, Goldmont, or later;
Windows 10 RS3 operating system (version 1709) or later. To check the system version, use the winver command.
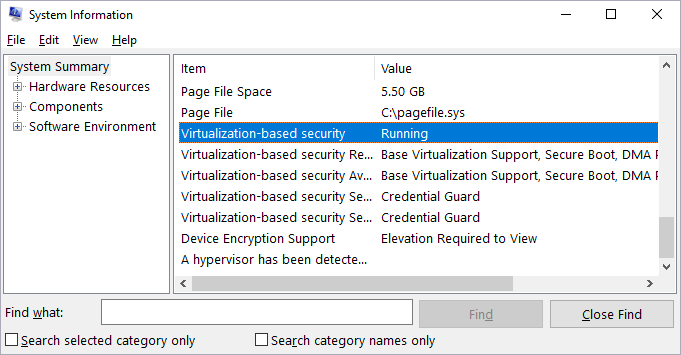
Run the msinfo32 command to make sure the Hyper-V is enabled and running.
The System Summary in the System Information dialog box should show the Virtualization-based security item as Running:
If your system does not meet the profiling requirements but you plan to run hardware event-based sampling analysis with VTune Profiler, make sure to disable the Hyper-V feature in the system settings.
Disable the Credential Guard and Device Guard on Hyper-V
The Hyper-V has optional security features: Device Guard and Credential Guard. When either or both of them are enabled, accessing non-architectural PMU MSRs triggers (required for the driver-based hardware event sampling analysis) a general protection fault. For example, offcore response MSRs and uncore related MSRs are non-architectural MSRs. To collect these events, you must disable the security features as follows:
Make sure the security features are running on your system:
Run the msinfo32 command to open the System Information dialog.
In the System Summary, check whether the Virtualization-based Security Services Running item includes Hypervisor enforced Code Integrity and/or Credential Guard values.
Disable these security features by running the Microsoft* DG-CG-Readiness-Tool, available at https://www.microsoft.com/en-us/download/details.aspx?id=53337:
Open Powershell as an administrator and go to the tool installation directory.
Run the tool as follows:
.\DG_Readiness_Tool_v2.1.ps1 -Disable -CG -DGReboot the system.
Make sure the device guard is turned off. The output from msinfo32 should NOT include either Hypervisor enforced Code Integrity or Credential Guard.