Intel® Active Management Technology 11
Getting Started with Intel AMT
In order to manage an Intel® Active Management Technology (Intel® AMT) client or run the samples from the SDK, you will need to use a secondary system as a management console to remotely manage your Intel AMT device. Refer to the Intel AMT Implementation and Reference Guide for more details.
What is Intel Active Management Technology?
Intel AMT is part of the Intel® vPro™ technology offering. Platforms equipped with Intel AMT can be managed remotely, regardless of their power state or whether or not they have a functioning OS.
The Intel® Converged Security and Manageability Engine (Intel CSME) is a key component of an Intel AMT device. As a component of the Intel® vPro™ platform, Intel AMT uses a number of elements in the Intel vPro platform architecture. Figure 1 shows the relationship between these elements.
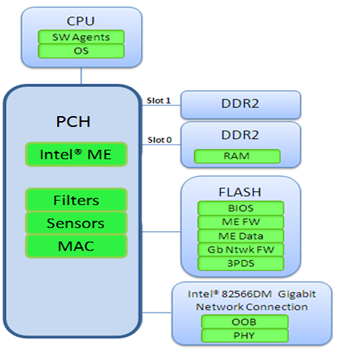
Figure 1. Intel® Active Management Technology 11 architecture.
Note: The Intel CSME is the new name for the Intel® Manageability Engine (Intel® ME).
Pay attention to the network connection associated with the Intel ME. Note that the NIC changes according to which Intel AMT release is on the device.
- The Intel CSME firmware contains the Intel AMT functionality.
- Flash memory stores the firmware image.
- Enable the Intel AMT capability by using the Intel CSME as implemented by an OEM platform provider. A remote application is used to perform the enterprise setup and configuration.
- On power-up, the firmware image is copied into the Double Data Rate (DDR) RAM.
- The firmware executes on the Intel® processor with Intel CME and uses a small portion of the DDR RAM (Slot 0) for storage during execution. RAM slot 0 must be populated and the system must be connected to power for the firmware to run.
Intel AMT stores the following information in flash (Intel CSME data):
- OEM-configurable parameters:
- Setup and configuration parameters such as passwords, network configuration, certificates, and access control lists (ACLs)
- Other configuration information, such as lists of alerts and Intel AMT System Defense policies
- The hardware configuration captured by the BIOS at startup
- Details for the 2016 platforms with Intel vPro technology (Release 11.x):
- 14nm process
- Platform (mobile and desktop): 6th generation Intel® Core™ processor
What is New With the Intel Active Management Technology SDK Release 11.0
- The Intel CSME is the new architecture for Intel AMT 11. Prior to Intel AMT 11, CSME was called the Intel® Management Engine BIOS Extension (Intel® MEBX).
- MOFs and XSL files: The MOFs and XSL files in the \DOCS\WS-Management directory and the class reference in the documentation are at version 11.0.0.1139.
- New WS-Eventing and PET table argument fields: Additional arguments added to the CILA alerts provide a reason code for the UI connection and the hostname of the device that generates the alert.
- Updated OpenSSL* version: The OpenSSL version is at v1.0. The redirection library has also been updated.
- Updated Xerces version: Both Windows* and Linux* have v3.1.2 of the Xerces library.
- HTTPS support for WS Events: Secure subscription to WS Events is enabled.
- Remote Secure Erase through Intel AMT boot options: The Intel AMT reboot options have an option designed to securely erase the primary data storage device.
- DLL signing with strong name: The following DLLs are now signed with a strong name: CIMFramework.dll, CIMFrameworkUntyped.dll, DotNetWSManClient.dll, IWSManClient.dll, and Intel.Wsman.Scripting.dll
- Automatic platform reboot triggered by HECI and Agent Presence watchdogs: An option to automatically trigger a reboot whenever a HECI or Agent Presence watchdog reports that its agent has entered an expired state.
- Replacement of the IDE-R storage redirection protocol: Storage redirection works over the USB-R protocol rather than the IDE-R protocol.
- Updated SHA: The SHA1 certificates are deprecated, with a series of implemented SHA256 certificates.
Configuring an Intel Active Management Technology Client
Preparing your Intel AMT client for use.
Figure 2 shows the modes, or stages, that an Intel AMT device passes through before it becomes operational.
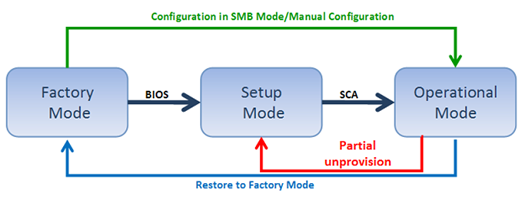
Figure 2. Configuration flow of an Intel® Active Management Technology device.
Before configuring an Intel AMT device from the Intel SCS, it must be prepared with initial setup information and placed into Setup Mode. The initial information will be different depending on the available options in the Intel AMT release, and the settings performed by the platform OEM. Table 1 summarizes the methods to perform setup and configuration on the different releases of Intel AMT.
| Setup Method | Applicable to Intel® Active Management Technology Releases | For More Information |
|---|---|---|
| Manual | 6.0 and later | Manual Setup and Configuration (from Release 6.0) |
| CCM, ACM | 7.0 and later |
Table 1. Setup methods according to Intel® Active Management Technology version.
Intel® Setup and Configuration Software (Intel® SCS) 11 can provision systems back to Intel AMT 2.x. For more information about Intel SCS and provisioning methods as they pertain to the various Intel AMT releases, visit Download the latest version of Intel® Setup and Configuration Service (Intel® SCS).
Manual Configuration Tips
There are no feature limitations when configuring a platform manually since the 6.0 release, but there are some system behaviors to be noted:
- API methods will not return a PT_STATUS_INVALID_MODE status because there is only one mode.
- TLS is disabled by default and must be enabled during configuration. This will always be the case with manual configuration as you cannot set TLS parameters locally.
- The local platform clock will be used until the network time is remotely set. An automatic configuration will not be successful unless the network time was set (and this can only be done after configuring TLS or Kerberos*). Enabling TLS or Kerberos after the configuration will not work if the network time was not set.
- The system enables WEB UI by default.
- The system enables SOL and IDE-R by default.
- The system disables Redirection listener by default starting in Intel AMT 10.
- If KVM is enabled locally via the Intel CSME, it still will not be enabled until an administrator activates it remotely.
Starting with Intel AMT 10, some devices are shipped without a physical LAN adapter. These devices cannot be configured using the current USB Key solutions provided by Intel SCS 11.
Manual Setup
During power up, the Intel AMT platform displays the BIOS startup screen, then it processes the Intel MEBX. During this process, access to the Intel MEBX can be made; however, the method is BIOS vendor-dependent. Some methods are as follows:
- Most BIOS vendors add entry into the Intel CSME via the boot menu. Select the appropriate key (Ctrl+P is typical) and follow the prompts.
- Some OEM platforms prompt you to press <Ctrl+P> after POST. When you press <Ctrl+P>, control passes to the Intel MEBX (CSME) main menu.
- Some OEMs integrate the CSME configuration inside the BIOS (uncommon).
- Some OEMs have an option in the BIOS to show/hide the <Ctrl+P> prompt, so if the prompt is not available in the one-time boot menu check the BIOS to activate the Ctrl+P.
Client Control Mode and Admin Control Mode
At setup completion, Intel AMT 7.0 and later devices go into one of two control modes:
- Client Control Mode. Intel AMT enters this mode after performing a basic host-based setup (see Host-Based (Local) Setup). It limits some of the Intel AMT functionality, reflecting the lower level of trust required to complete a host-based setup.
- Admin Control Mode. After performing remote configuration, USB configuration, or a manual setup via the CSME, Intel AMT enters Admin Control Mode.
There is also a configuration method that performs an Upgrade Client to Admin procedure. This procedure presumes the Intel AMT device is in Client Control Mode, but moves the Intel AMT device to Admin Control Mode.
In Admin Control Mode there are no limitations to Intel AMT functionality. This reflects the higher level of trust associated with these setup methods.
Client Control Mode Limitations
When a simple host-based configuration completes, the platform enters Client Control Mode and imposes the following limitations:
- The System Defense feature is not available.
- Redirection (IDE-R and KVM) actions (except initiation of an SOL session) and changes in boot options (including boot to SOL) require advanced consent. This still allows remote IT support to resolve end-user problems using Intel AMT.
- With a defined Auditor, the Auditor’s permission is not required to perform un-provisioning.
- Several functions are blocked to prevent an untrusted user from taking control of the platform.
Manually Configuring an Intel Active Management Technology 11.0 Client
The Intel AMT platform displays the BIOS startup screen during power up, then processes the BIOS Extensions. Entry into the Intel AMT BIOS Extension is BIOS vendor-dependent.
If you are using an Intel AMT reference platform (SDS or SDP), the display screen prompts you to press <Ctrl+P>. Then the control passes to the Intel CSME main menu.
In the case of it being an OEM system, it is still easy to use the one-time boot menu, although entry into the Intel CSME is usually included as an option as part of the one-time boot menu. The exact key sequence varies by OEM, BIOS, and model.
Manual Configuration for Intel AMT 11.0 Clients with Wi-Fi*-Only Connection
Many systems no longer have a wired LAN connector. You can configure and activate the Intel CSME, then use a Web UI or some alternate method to push the wireless settings.
- Change the default password to a new value (required to proceed). The new value must be a strong password. It should contain at least one upper-case letter, one lower-case letter, one digit, and one special character, and be at least eight characters.
- Enter the Intel CSME during startup.
- Enter the Default Password of “admin.”
- Enter and confirm New Password.
- Select Intel AMT Configuration.
- Select/Verify Manageability Feature Selection is Enabled.
- Select Activate Network Access.
- Select “Y” to confirm activating the interface.
- Select Network Setup.
- Select Intel® CME network Name Settings.
- Enter Host Name.
- Enter Domain Name.
- Select User Consent.
- By default, this is set for KVM only; it can be changed to none or all.
- Exit the Intel CSME.
- Configure Wireless via the Intel® PROSet/Wireless Driver profile synching, Web UI, or an alternative method.
Manual Configuration for Intel AMT 11.0 Clients with LAN Connection
Enter the CSME default password (“admin”).
Change the default password (required to proceed). The new value must be a strong password. It should contain at least one upper-case letter, one lower-case letter, one digit, and one special character, and be at least eight characters. A management console application can change the Intel AMT password without modifying the CSME password.
Accessing Intel Active Management Technology via the Web UI
An administrator with user rights can remotely connect to the Intel AMT device via the Web UI by entering the URL of the device. Depending on whether TLS has been activated, the URL will change:
You can also use a local connection using the host’s browser for a non-TLS connection. Use either localhost or 127.0.0.1 as the IP address. Example: http://127.0.0.1:16992
Intel Active Management Technology Support Requirements
In addition to having the BIOS and the Intel CSME configured correctly, the Wireless NIC needs to be Intel AMT compliant. Specific drivers and services must be present and running in order to use the Intel AMT to manage the host OS.
To verify that the Intel AMT drivers and services are loaded correctly, look for them in the Device Manger and Services in the host OS. Frequently check the OEM’s download site for upgraded versions of the BIOS, firmware, and drivers.
Here are the drivers and services that should appear in the host:
* Network controller and wireless interface versions will vary depending on the generation of the Intel vPro platform.
** Part of the complete Intel MEI (Chipset) Driver package.
*** HID drivers are needed when connecting via Intel AMT KVM. These default drivers are not normally an issue; however, we have seen issues on stripped-down custom OS installs. If a connection is made to a device without the HID drivers, the OS tries to auto-download the drivers. Once the install is done, reconnect the KVM connection.
Note: The version level of the drivers must match the version level of the firmware and BIOS. If non-compatible versions are installed, Intel AMT will not work with the features that require those interfaces.
Physical Device - Wireless Ethernet Connection
By default, any wireless Intel vPro platform will have an Intel AMT-enabled wireless card installed, such as an Intel Dual Band Wireless-AC 8260. Any wireless card other than one from Intel will not have wireless Intel AMT capabilities. If you have a card other than the Intel Dual Band Wireless-AC 8260, you can access ark.intel.com to verify whether the wireless card is Intel AMT compliant.
Windows* OS Required Software
Device drivers are not necessary for remote management; however, they are essential for local communication to the firmware. Functions like discovery or configuration via the OS will require the Intel MEI driver, SOL driver, Local Manageability Service (LMS) and Intel® MSS.
Device Drivers - Intel® Management Engine Interface
The Intel CSME is required to communicate to the firmware. The Windows automatic update installs the Intel MEI driver by default. The Intel MEI driver should stay in version step with the Intel MEBX version.
The Intel CSME driver is in the Device Manager under “System devices” as “Intel Management Engine Interface.”
Device Drivers - Serial-Over-LAN Driver
The SOL driver used during the redirection operation where a remote CD drive is mounted during an IDE redirection operation.
The SOL driver is in the Device Manager under “Ports” as “Intel® Active Management Technology – SOL (COM3).”
Figure 3. Serial-Over-LAN driver.
Service - Intel Active Management Technology LMS
The LMS runs locally in an Intel AMT device and enables local management applications to send requests and receive responses. The LMS responds to the requests directed at the Intel AMT local host and routes them to the Intel ME via the Intel MEI driver. This service installer is packaged with the Intel MEI drivers on the OEM websites.
Please note that when installing the Windows OS, the Windows Automatic Update service installs the Intel MEI driver only. IMSS and the LMS are not installed. The LMS communicates from an OS application to the Intel MEI driver. If the LMS is not installed, go to the OEM website and download the Intel CSME driver, which is usually under the Chipset Driver category.
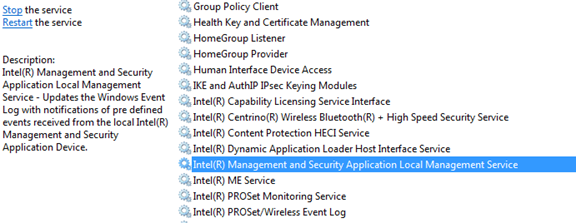
Figure 4. Intel® Management Engine Interface driver.
The LMS is a Windows service installed on the host platform that has Intel AMT Release 9.0 or greater. Prior to this, the LMS was known as the User Notification Service (UNS) starting from Intel AMT Release 2.5 to 8.1.
The LMS receives a set of alerts from the Intel AMT device. LMS logs the alert in the Windows Application event log. To view the alerts, right-click My Computer, and then select Manage>System Tools>Event Viewer>Application.
Tool - Intel® Management and Security Status Tool
The Intel MSS tool can be accessed by the blue-key icon in the Windows tray.
Figure 5. System Tray Intel® Management and Security Status icon.
Intel Active Management Technology Software Development Kit
The Intel AMT Software Development Kit (SDK) provides low-level programming capabilities so developers can build manageability applications that take full advantage of Intel AMT.
The Intel AMT SDK provides sample code and a set of APIs that let developers easily and quickly incorporate Intel AMT support into their applications. The SDK also includes a full set of HTML documentation.
The SDK supports C++ and C# on Microsoft Windows and Linux operating systems. Refer to the user guide and the Readme files in each directory for important information on building the samples.
The SDK, as delivered, is a set of directories that can be copied to any location. The directory structure should be copied in its entirety due to the interdependencies between components. There are three folders at the top level: DOCS (contains SDK documentation) and one each for Linux and Windows (sample code). For more information on how to get started and how to use the SDK, see the Intel® AMT Implementation and Reference Guide.
As illustrated by the screenshot in Figure 9 of the Intel AMT Implementation and Reference Guide, you can get more information on system requirements and how to build the sample code by reading the Using the Intel® AMT SDK section. The documentation is available on the Intel® Software Network here: Intel® AMT SDK (Latest Release).
Figure 9. Intel® AMT Implementation and Reference Guide.
Other Intel Active Management Technology Resources
Intel AMT Implementation and Reference Guide Intel AMT SDK download Intel AMT High-level API article and download Intel vPro Platform Solutions Manager article and download Intel vPro Technology module for Windows* PowerShell downloadKVM Application Developer’s GuideRedirection LibraryC++ CIM Framework APIC# CIM Framework APIIntel ME WMI ProviderSystem Health Validation (NAP)Use Case Reference Designs
Appendix
The following table provides a snapshot of features supported by Intel® AMT Releases 8 through 11.
Read about all the features in the Intel AMT SDK Implementation and Reference Guide (“Intel AMT Features” section.)
| Feature | Intel® Active Management Technology (Intel® AMT) 8 | Intel AMT 9 | Intel AMT 10 | Intel AMT 11 |
|---|---|---|---|---|
| Hardware Inventory | X | X | X | X |
| Persistent ID | X | X | X | X |
| Remote Power On/Off | X | X | X | X |
| SOL/IDER | X | X | X | X |
| Event Management | X | X | X | X |
| Third-Party Data Storage | X | X | X | Deprecated |
| Built-in Web Server | X | X | X | X |
| Flash Protection | X | X | X | X |
| Firmware Update | X | X | X | X |
| HTTP Digest/TLS | X | X | X | X |
| Static and Dynamic IP | X | X | X | X |
| System Defense | X | X | X | X |
| Agent Presence | X | X | X | X |
| Power Policies | X | X | X | X |
| Mutual Authentication | X | X | X | X |
| Kerberos* | X | X | X | X |
| TLS-PSK | X | X | X | Deprecated |
| Privacy Icon | X | X | X | X |
| Intel® Management Engine Wake-on-LAN | X | X | X | X |
| Remote Configuration | X | X | X | X |
| Wireless Configuration | X | X | X | X |
| Endpoint Access Control (EAC) 802.1 | X | X | X | X |
| Power Packages | X | X | X | X |
| Environment Detection | X | X | X | X |
| Event Log Reader Realm | X | X | X | X |
| System Defense Heuristics | X | X | X | X |
| WS-MAN Interface | X | X | X | X |
| VLAN Settings for Intel AMT | X | X | X | X |
| Network Interfaces | X | X | X | X |
| Fast Call For Help (CIRA) | X | X | X | X |
| Access Monitor | X | X | X | X |
| Microsoft NAP* Support | X | X | X | X |
| Virtualization Support for Agent Presence | X | X | X | X |
| PC Alarm Clock | X | X | X | X |
| KVM Remote Control | X | X | X | X |
| Wireless Profile Synchronization | X | X | X | X |
| Support for Internet Protocol Version 6 | X | X | X | X |
| Host-Based Provisioning | X | X | X | X |
| Graceful Shutdown | X | X | X | X |
| WS-Management API | X | X | X | X |
| SOAP Commands | X | Deprecated | Deprecated | Deprecated |
| InstantGo Support | N/A | N/A | N/A | X |
| Remote Secure Erase | N/A | N/A | N/A | X |
*No product or component can be absolutely secure.