This information is correct as of the original publishing date. Subsequent advances in technology may result in different instructions being needed.
Intel Fellow Client Computing Group
Intel has a long history of working with the software community and making strides in strengthening protections of operating systems and software running on modern computer systems. As these protections came into effect, adversaries started looking for creative alternatives to bypass these protections. Return-oriented programming (ROP) and jump-oriented programming (JOP) are two such techniques that have been gaining popularity. JOP or ROP attacks can be particularly hard to detect or prevent because the attacker uses existing code running from executable memory in a creative way to change program behavior. What makes it hard to detect or prevent ROP and JOP is the fact that the attacker uses existing code running from executable memory. Many software-based detection and prevention techniques have been developed and deployed with limited success.
ROP is where the attacker relies on return (RET) instruction to stitch together a malicious code flow that was not programmer-intended. Per the design, RET instructions fetch the address of the next instruction from stack (which was pushed on the stack by the prior CALL instruction) and executes instructions from that address. In the case of ROP-based attacks, at runtime the attacker scans for sequence of bytes in existing program code by scanning the program on disk or in memory. Figure 1 shows an example of existing instruction stream.
Figure 1
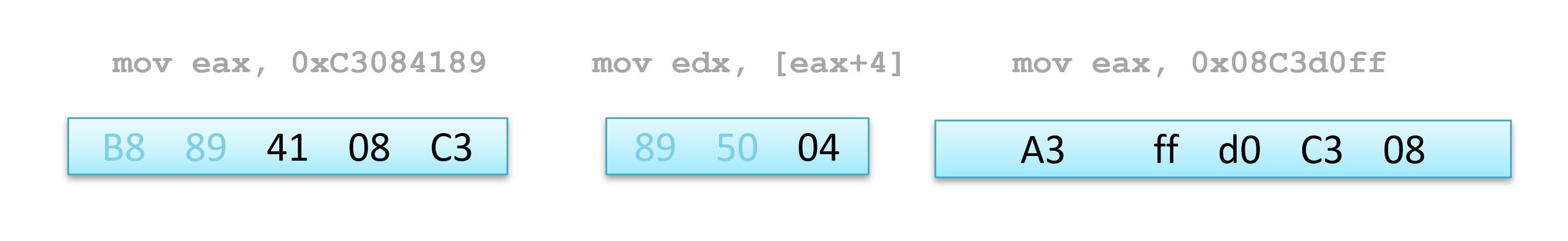
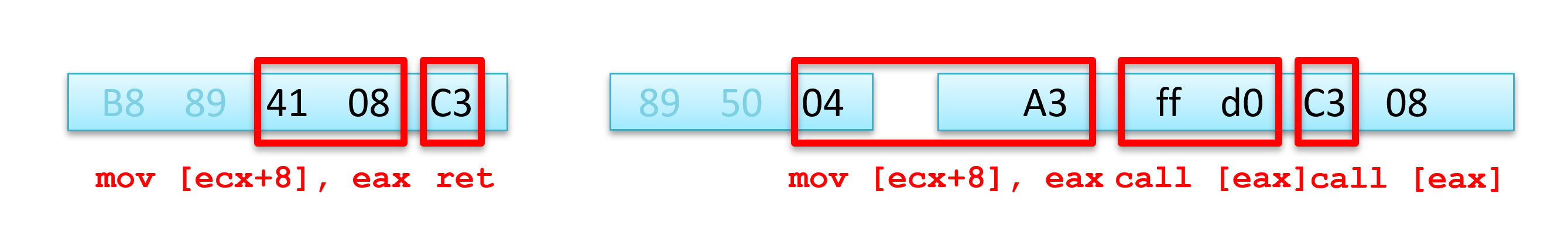
This example shows three instructions run in a sequence (notice there are no RET instructions in this programmer-intended sequence) and the corresponding bytes of program in blue boxes below. The same set of code bytes, when interpreted starting at an invalid offset, can also mean an alternate set of instructions that cause the sequence to end with a RET, as shown in the figure below where bytes in red boxes correspond to a different instruction sequence. In this example, each instruction is followed by C3, which corresponds to the return instruction. These instruction sequences are called “gadgets.”
Figure 2
By carefully placing starting addresses of these alternate instruction-sets or “gadgets” that are all terminated by the RET instruction, the attacker can execute arbitrary attack code flows that were not intended in the original program using already-executable bytes of the original program. So, with a ROP attack, the attacker can run arbitrary code composed via gadgets using the existing program inheriting all the permissions of the program. This makes these attacks effective and hard to detect and potentially allows an attacker to escalate privileges or break out of process sandboxes. These types of malware target operating systems, browsers, readers, and many other applications, and it takes deep integration with hardware at the foundation to deliver more effective protection with minimal performance impact.
Since ROP relies on RET instructions, where the address of the next instruction to run is fetched from a stack, stack corruption plays a critical role in ROP attacks. Intel® Control-Flow Enforcement Technology (Intel® CET) enables the operating system to create a shadow stack, which is designed to be protected from application code memory accesses and stores CPU-stored copies of the return addresses. This helps ensure that even when an attacker is able to modify or corrupt the return addresses in the data stack for the purpose of carrying out a ROP attack, the attacker is not able to modify the shadow stack, and the Intel CET state machine in the CPU detects mismatches between the address on the shadow and data stack to help prevent the attack through an exception reported to the operating system.
Similarly, other indirect branch instructions, such as CALL and JUMP indirect can be used to launch variant attacks—call oriented programming (COP) or JOP. Intel CET also adds an indirect branch tracking capability to provide software the ability to restrict COP and JOP attacks.
Intel has been actively collaborating with Microsoft* and other industry partners to address control-flow hijacking by using Intel CET technology to augment the previous software-only control-flow integrity solutions. Intel CET, when used properly by software, is a big step in helping to prevent exploits from hijacking the control-flow transfer instructions. For more details, reference Understanding Hardware-Enforced Stack Protection.
Reference Links
Intel® Software Development Emulator (Intel® SDE)
GNU Compiler Collection (GCC)* Instrumentation Options
Linux* Kernel Patches