In this article, we use ssh to connect to a remote system and run a demo, Security Barrier Camera. The demo will be launched on the IEI Tank* AIoT Developer Kit (target) running Linux* from the Developer Workstation (host).
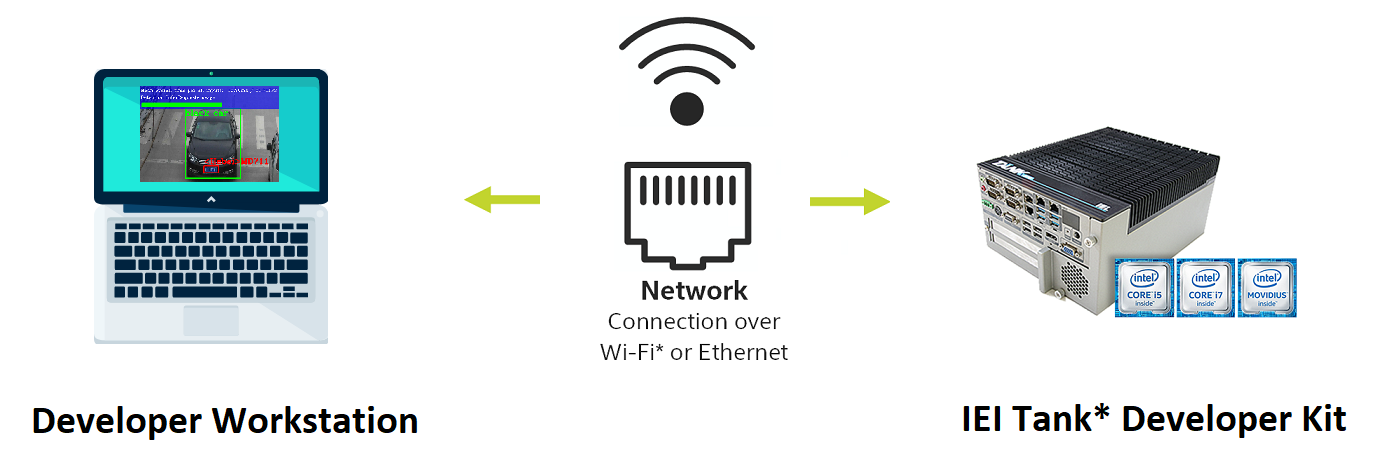
When you run the demo, the command will run on the target from the host and the results will return to the host machine using X forwarding.
Terminology
| Term | Description |
| Host Device | Your Development Environment Machine - For example, your dev laptop or dev desktop machine |
| Target Device | IEI Tank* AIoT Developer Kit |
| ssh | Secure Shell |
| scp | Not recommended per OpenSSH: secure copy protocol |
| rsync | remote sync - an open source utility that provides fast incremental file transfer |
| sftp | SSH File Transfer Protocol or Secure File Transfer Protocol |
For this article, the following recommended requirements are listed in the table below.
Requirements
Host Device Requirements |
|
||||
Target Device Requirements |
|
||||
Knowledge Requirement |
To install and run the demo application, you will need: Familiarity with Linux* commands |
In this article, we will explore using ssh server to remotely run the toolkit demo. The host and target in this example are on the same network.
| Step 1: Setup SSH Connection Between Target and Host | Setup SSH. Connect via ssh to the target. |
| Step 2: Run the Security Barrier Demo Remotely from Host Development Environment - CPU | Open Security Barrier Demo Remotely using your Host Machine to run on Target, returning image result on your Host |
| Step 3: Run the Security Barrier Demo Remotely from Host Development Environment - GPU | Run on GPU using -d GPU |
Security Barrier Camera Demo
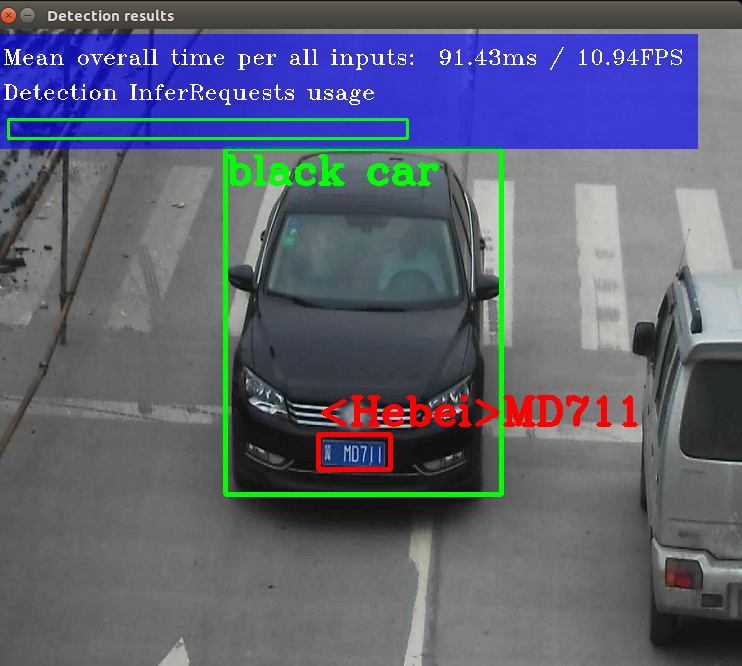
The demo you will run is the Security Barrier Camera Demo included in the Intel® Distribution of OpenVINO™ toolkit. This demo runs multiple deep learning models, including license plate detection, vehicle attributes, and license plate recognition.
The host system connected to the target system, will be used to run the demo.
Note: The security barrier demo is located at /opt/intel/openvino/deployment_tools/demo
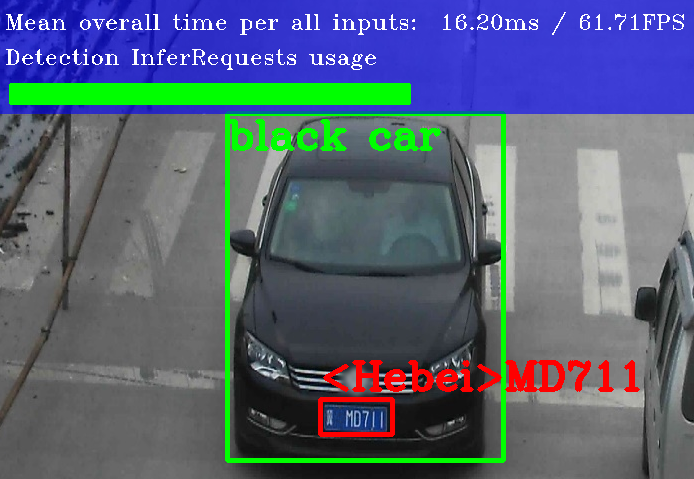
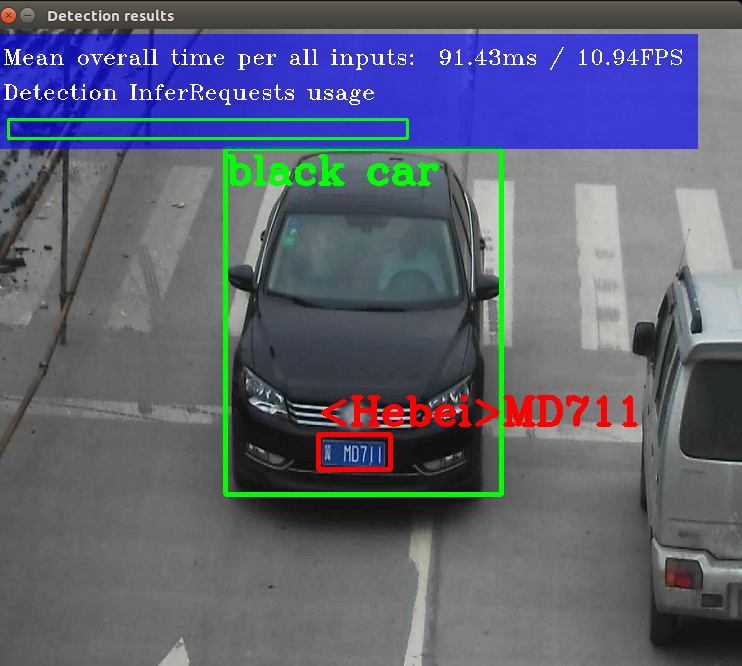
Below is an example of the security barrier demo output.
Step 1: Setup a SSH Connection Between the Target and Host
In this step you will be setting up a Secure Shell (SSH) connection between your host and target systems. This connection is required. This example scenario includes physical access to the target for setup.
Physical access: Connect a keyboard, monitor, and mouse to your target system.
- Connect your target system to same network as your host system.
- On your target system, install openssh-server. This is not installed by default.
sudo apt-get install openssh-server - Obtain the IP address of the target system (IEI Tank*) using ip or ifconfig:
ip a
Once the target machine IP address is discovered, you can connect via ssh.
From the host system, test the SSH connection.
Use the flag X to enable X11 forwarding. The -X flag in the ssh command allows X11 from your target to display an output on your host.
ssh -X username@IPADDRESS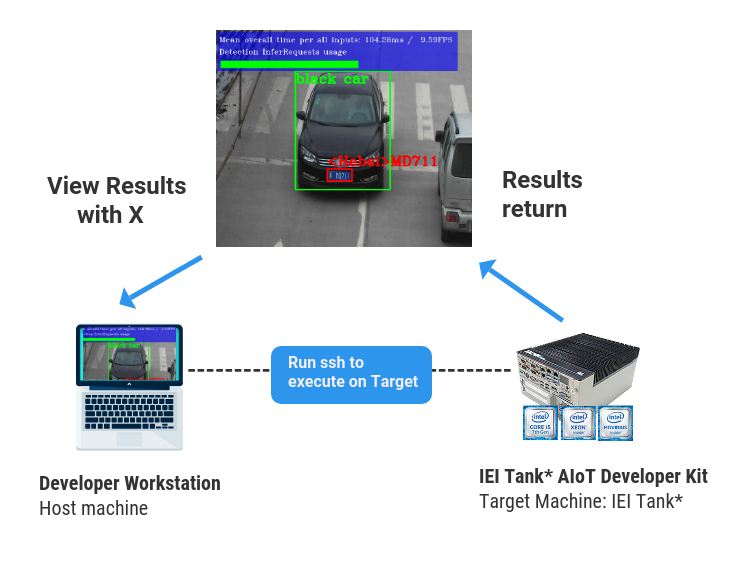
When prompted enter the password of the user.
Troubleshooting Tip
If you get an error:
-
Verify the two systems are on the same network. Try pinging the target from the host, and the host from the target.
-
Verify the ssh service is running on the target
sudo service ssh statusIf it’s not running, restart the service.
sudo service ssh restart
Note: Without physical access, there are a few ways to discover the IP: Running a port scan, or if you have router access, you can use this to discover the IP address.
Step 2: Run the Security Barrier Camera Demo - CPU
The Security Barrier demo script in the Intel® Distribution of OpenVINO™ toolkit:
- initializes the environment
- downloads the models
- runs the security barrier demo
The results display using the car image provided in the demo directory. Since we used the -X flag when the ssh connection was established, we will see the results on the host system.
- Run this command in the terminal to change to the demo directory.
cd /opt/intel/openvino/deployment_tools/demo - Run the following command to run the demo
./demo_security_barrier_camera.sh
The results display with a car being identified in the frame with an overlay of the frames per second.
Because the target device is set at run-time, you can use the same binary to run on CPU, GPU, or other Intel® Vision Accelerator Design product. Run the same demo, but with the GPU to compare performance.
Step 3: Run the Security Barrier Demo - GPU
- Run the following command to run the demo
./demo_security_barrier_camera.sh -GPU
2. Results display on the host. The results are similar to the image below.