Introduction – Wide-Area Networks (WAN) Contribution to the Growing Attack Surface
It is often said that complexity is the enemy of security. The reason for this is very simple.
Attackers work by continuously probing attack surfaces in search of "seams," or weaknesses, in the IT infrastructure. These could be places where there is human interaction, where there is control hand-off and opportunity for error, where invisible infrastructure touches an open network, or where operational information inadvertently reveals potential exploits. It's simple math. Larger and more complex attack surfaces offer more opportunities for attackers to get inside.
There was a time when minimizing the size and complexity of networks made good management and security sense. Then came the cloud, low-cost internet connectivity, mobility, the internet of Things (IoT); suddenly, networks have become anything but simple.
For example, take an ordinary database application that at one time would have run securely inside a corporate data center. Today, pieces of that solution might be scattered around the globe. You might have data storage from one cloud service provider, an analytics engine from another, access governance from another, and business logic provided by another. You might even have widely distributed connected devices feeding data directly into the database.
To further complicate this security picture, you also have WAN services that connect you to all your distributed assets and that connect the assets to each other. The combination of cloud services, mobility, and low-cost internet WAN has produced explosive growth in the size and complexity of networks and their attack surfaces. From the attackers' perspective, it's open season, and the conditions are perfect!
Protecting digital assets in this environment involves applying traditional layered strategies to new network architectures, building security into applications, and using new tools to secure endpoints. There is another part of the infrastructure that does not get the security attention it deserves. That is WAN connectivity, which is increasingly becoming the fabric that holds together the entire distributed enterprise.
As the one piece of infrastructure that touches all those distributed digital assets, the WAN is an important part of the attack surface, but it may also be the foundation for a more comprehensive approach to securing complex IT infrastructures. Yet people making decisions about WAN services typically focus on cost and performance. Security of the WAN itself is too often a secondary consideration.
In an earlier article How Netrolix Broke the SD-WAN Barrier with AI-WAN*, we showed how Netrolix has developed a new approach to wide-area networking. It is an artificial intelligence (AI)-driven internet network, an AI-WAN, that has the cost and agility advantages of software-defined wide-area networking (SD-WAN), the quality of service guarantees of private line solutions, and security that is superior to both.
In this article, we dig deeper into Netrolix AI-WAN* security advantage. But before doing that, let's look closely at the security strengths and weaknesses of the two most common WAN solutions: Multiprotocol Label Switching (MPLS) private lines and SD-WAN.
Private Infrastructure and MPLS – Private, but Secure?
From a performance, reliability, and security perspective, private connections are typically considered the ideal WAN solution. MPLS has become one of the most widely used data-carrying methods in private infrastructure because of its ability to carry a variety of network protocols and access technologies, simplifying the configuration of multipurpose private connections.
However, these connections are expensive and inflexible. They need to be configured by service providers, which sometimes takes months, and their cost is too high to support all the demand for wide-area networking. Many organizations reserve private connections for their most critical operations and use public infrastructure to fill less sensitive WAN needs.
This decision is based in part on the assumption that private connections are more secure. But are they really?
The idea is that because private lines are private, they provide no visibility to potential attackers, and therefore they are proof against outside attack. Being so invulnerable, they were never designed to natively support data-protection methods like encryption. Of course, if a service provider's core network were ever breached, all that unencrypted data would be exposed.
But that's not the only way MPLS connections can be compromised. Private MPLS circuits often use a layer-2 connection from a local incumbent service provider to send unprotected data across many miles and multiple facilities until it is handed off to the MPLS provider. This is done because, in the case of a customer with widely distributed locations, no single provider has the extended geographical footprint to directly connect all the locations using just its own assets. For example, when service provider A delivers MPLS services in service provider B's territory, provider A purchases backhaul connectivity from provider B back to the agreed upon colocation point. This way of delivering private MPLS connections creates a very easy and well-known man-in-the-middle attack surface.
The only way to protect against these kinds of MPLS attacks is to encrypt data, but alas, MPLS does not natively support encryption. To encrypt data passing through MPLS private connections, every single application, wherever it is located in the complex, highly distributed infrastructure, must encrypt its data. This can be a big management task with lots of room for error, especially in a complex network infrastructure.
Public Infrastructure and SD-WAN – The Devil Is In the Details
WAN connections over public infrastructure rely on the internet to transport data, and it's this internet connection that worries security managers. There's too much visibility and complexity to assure data security in the vastness of the global internet. That's why WAN solutions using public infrastructure often include data encryption.
For example, SD-WAN is one form of internet WAN that many organizations are adopting to fill their growing need for more WAN connectivity. Although SD-WAN doesn't deliver the quality of service of a private line, it is easier to set up and costs much less. Many contend that SD-WAN is more secure than MPLS because it natively supports data encryption, which makes it easy to encrypt all data moving in the network, regardless of where the data is coming from.
This sounds great, but as is often the case, it's not the whole story. SD-WAN has real and potential vulnerabilities that need to be considered, including:
- SD-WAN's low cost and ease of deployment make it possible to expand your WAN quickly, which means that more assets can be moved into the cloud and new services can be easily added for partners and customers. All of this creates rapid growth in network size, complexity, and attack surface.
- Not all data encryption provides the same level of protection. Some providers use less challenging encryption algorithms to save on computational cost. The types of encryption keys and re-keying practices can also affect the strength of encryption.
- SD-WAN appliances used by many service providers contain known vulnerabilities, and they do not have adequate protection from administrative or physical access. Because of the way SD-WANs operate, compromising one SD-WAN appliance can provide access to an entire network. As SD-WANs grow, the risk from vulnerable appliances also grows. Since there is no private core network connectivity in most SD-WANs, the individual and unique peer-to-peer connections required to make them work offer no way of seeing or detecting abnormal behavior.
Netrolix AI-WAN – More Secure Than SD-WAN and MPLS
As detailed in an earlier article about Netrolix AI-WAN (How Netrolix Broke the SD-WAN Barrier with AI-WAN*), the Netrolix AI-WAN consists of the AI-WAN fabric, which is a vast network of ISPs and host data centers around the globe whose traffic is continuously analyzed and monitored by a proprietary deep-learning analytical engine.
Netrolix accomplishes this by having hardware and software installed in 70 data centers globally and collecting internet data from 20,000 nodes. This enables continuous analysis of multiple performance factors on all the ISPs on the planet to determine optimal data paths to any endpoint and across the Netrolix AI-WAN core.
To connect to this AI-WAN fabric, Netrolix has developed a suite of low-cost endpoint devices, which are software-defined gateways (SDGs) that run on either their own Intel® architecture-based bare-metal platforms, or appropriate client-owned equipment. The AI engine monitors the global internet while monitoring and communicating with every endpoint device connected to the AI-WAN fabric. All of Netrolix's services, including MPLS, Virtual Private LAN Service (VPLS), Ethernet private line, SD-WAN, global Virtual Private Network (VPN), cloud services, and other offerings are layered over the AI-WAN fabric.
This enables Netrolix to deliver WAN performance that is on par or better than traditional private networks from global service providers, with guaranteed throughput at wire speeds, much lower cost, and all with the flexibility and ease of setup that an SD-WAN offers.
There is another big advantage to Netrolix AI-WAN. It provides a level of WAN security that is unmatched by SD-WAN or MPLS services. Let's see why that is so.
Netrolix AI-WAN Defense in Depth
The Netrolix AI-WAN security posture addresses three aspects of network security:
- Securing data on the network
- Securing the AI-WAN fabric
- Integrating with or augmenting existing enterprise security
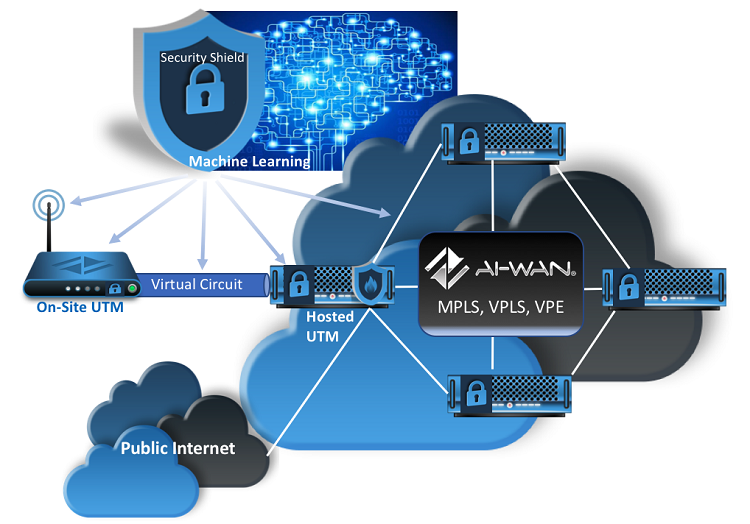
Netrolix uses defense in depth to secure the AI-WAN fabric while integrating with existing enterprise and cloud defenses.
Five factors that secure data on the AI-WAN network
Netrolix applies a multifactor security strategy for protecting data on the network that includes the following elements:
- Data encryption – All data passing through the Netrolix AI-WAN is automatically encrypted using IKEv2 elliptic curve cryptography, which is the most powerful encryption standard currently in use.
- Key management – The Netrolix AI-WAN uses a robust Key Management System (KMS) to generate encryption keys for every device, every element of the AI-WAN network, every storage instance, and every network configuration. Many SD-WAN providers use one encryption key across a network, and key swapping or re-keying is done manually. In that case, if a key is compromised in one location, the entire network is compromised. In the Netrolix AI-WAN, every network element has its own key, and every key in the global AI-WAN is automatically re-keyed every 30 minutes.
- Hardware Security Module (HSM) authentication – In the Netrolix AI-WAN, every Netrolix SDG uses HSM authentication, which is the same hardware-based authentication used in credit and debit card chips. It prevents access to the encryption keys of any Netrolix SDG unless the device is connected over the AI-WAN to a Netrolix management console, which prohibits unauthorized access.
- RADIUS attributes – These are used to authenticate any device that connects to the AI-WAN.
- The AI analytics engine – The Netrolix AI-WAN uses a proprietary deep-learning analytical engine that does several things. It analyzes global internet traffic and optimize end-to-end data paths from any device connected to the AI-WAN, across the AI-WAN core, to any endpoint (for details about this process, see How Netrolix Broke the SD-WAN Barrier with AI-WAN*). Every device connected to the AI-WAN gets data path re-optimization every five minutes.
The analytics engine also performs another important security function. It continuously monitors every device connected to the AI- WAN and identifies anomalous data patterns. It not only monitors the AI-WAN fabric itself, but also data coming from or going to devices connected to the AI-WAN, such as IoT devices, industrial control systems, or autonomous devices such as drones or robots, as an example. The ability to detect unusual network activity related to specific devices like these is an important capability. When these kinds of devices are added to an environment, they enlarge the attack surface. Yet many are being built with little understanding or regard for IT security.
Securing the AI-WAN fabric
In addition to protecting network data, several of the features described in the previous section also protect the AI-WAN fabric. For instance, by analyzing traffic associated with every device connected to the AI-WAN, the analytics engine is able to prevent someone from unplugging a device from the network and moving it to a new location. This change would immediately be detected and cause the device to be quarantined.
RADIUS functionality and IPSec prevent unauthorized devices from connecting to the network, and HSM prevents the compromise of the encryption keys. Beyond that, however, there are additional architectural features that harden the Netrolix AI-WAN.
For instance, it is not possible to locally manage a Netrolix SDG or gain visibility into a device by accessing the underlying operating system, for example. Access can only happen through a management console, and this is a containerized application that runs on a hypervisor in redundant centralized locations. All management functions executed by this console happen over IPSec using HSM authentication. With no access to the underlying architecture and no direct access to the hypervisor, Netrolix's SDGs become pretty impervious to unauthorized tampering.
The Netrolix SDGs are also protected against physical tampering. They were designed to be rigid boxes with no moving parts and no easy way to open. If a Netrolix SDG is forced open, its data is wiped with no possibility of recovery.
Total integration with enterprise layered security
The third key part of Netrolix AI-WAN security strategy is the way it is architected to easily integrate with an existing enterprise security stack. For instance, a Netrolix SDG can be configured as a simple network interface (NID). If a Netrolix AI-WAN user wants to keep their existing Fortinet, Juniper, Cisco, or whatever network devices they have in place today, those devices can connect to the AI-WAN through the Netrolix SDG configured as an NID.
But a Netrolix SDG can do more. It can work as a network access point plus a router, a switch, and a firewall, all in one solution. And it can be further configured with edge compute capabilities so that it combines network access, router, switch, firewall, and multi-access edge computing (MEC) in one solution.
Netrolix makes it very easy to configure their SDGs through the management console. When a new Netrolix SDG is plugged into your internet service, the AI-WAN immediately discovers it, optimizes it, begins encryption and key management, and enables its functions to be configured through the highly secure management console. This makes integration with existing security stacks an easy process.
How Intel Enables Netrolix AI-WAN Security
Netrolix considered several factors when choosing technology from Intel for the bare-metal platform that is the basis of all their SDGs. These considerations are detailed in an earlier article (How Netrolix Broke the SD-WAN Barrier with AI-WAN*).
Ultimately, it was the flexibility of chipsets from Intel in supporting Netrolix's architectural needs and the supporting software that were deciding factors. From the very beginning, designing an internet WAN that was more secure than any currently available public or private WAN option was central to those architectural needs.
The earlier article details chipsets used in different Netrolix SDG platforms, but several Intel technologies play an important role in supporting Netrolix's underlying AI-WAN security, including virtualization, secure hardware sharing, and hardware-based encryption. These include:
- Intel® Virtualization Technology (Intel® VT) for IA-32, Intel® 64 and Intel® Architecture (Intel® VT-x)
- Intel® Virtualization Technology (Intel® VT) for Directed I/O (Intel® VT-d) – secure hardware sharing
- Intel® Advanced Encryption Standard New Instructions (Intel® AES-NI) – CPU-based encryption
Netrolix AI-WAN Delivers a New Level of Internet WAN Security
One big challenge facing IT security managers today is that networks are growing so fast, traditional security practices are unable to keep up. In a world in which connected devices, distributed processing, and lots of internetworking are all happening beyond the direct control of those responsible for securing digital assets, WAN security is becoming fundamentally important.
Netrolix has created a new approach to internet WAN, an AI-WAN that is optimized and secured by a proprietary, deep-learning analytics engine. Netrolix's multifactor security strategy has effectively created a "defense in depth" approach to WAN security that does more than provide new levels of protection. It also extends WAN security beyond the wires to integrate with IT systems and existing enterprise security stacks. These are all the ways Netrolix AI-WAN makes wide-area networking more secure.
For More Information
- To learn more about the Netrolix AI-WAN and Netrolix's many networking services built on the AI-WAN fabric, see the article How Netrolix Broke the SD-WAN Barrier with AI-WAN.
- Visit the Netrolix website.
- Read the article Netrolix Harnesses the Net’s Wild Mustang: Optimized Internet & Private/Secure Service at Low Cost at the Top Operator website.
- Visit the Intel® Network Builders website and explore a vibrant resource center that provides support to anyone interested in software-defined networking and network function virtualization.