| Recent Revisions | |
|---|---|
| 2/8/2021 | Install the provisioning tool from Debian packages until a standalone version is available for Ubuntu* Linux* 20.04 |
| 2/3/2021 | Move to Ubuntu Linux 20.04 64-bit as the base OS |
Introduction
Intel® Software Guard Extensions Data Center Attestation Primitives (Intel® SGX DCAP) is Intel's solution for deploying Intel SGX attestation services into data centers. Because every data center environment has unique needs that require customization, it is distributed as a collection of components rather than a complete, turn-key solution. To help developers, data centers, and cloud service providers (CSP's) get started with Intel SGX DCAP, this article steps through the process of creating a minimal, but complete, Intel SGX DCAP environment. It produces a working infrastructure that is suitable for software developers who are creating Intel SGX solutions, and does so in a manner that mimics a real-world deployment to help data center administrators develop system deployment and management procedures.
For an introduction to Intel SGX DCAP, see the following white papers:
- Attestation for Data Center Orientation Guide
- Supporting Third Party Attestation for Intel® SGX with Intel® Data Center Attestation Primitives
And the following videos from Intel® Network Builders University (free registration required):
- Introduction to Intel® SGX Data Center Attestation Primitives
- Introduction to Intel® SGX Data Center Attestation Primitives: Components and Flows
- Intel® Software Guard Extensions Data Center Attestation Primitives: The Data Center Caching Service
The Minimum Environment
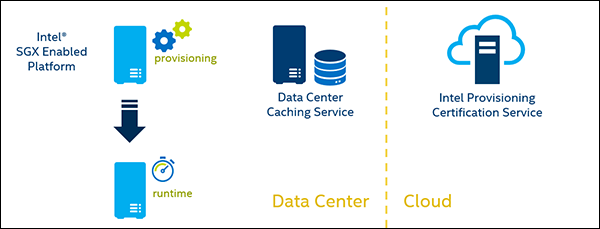
An Intel SGX DCAP Environment consists of three, fundamental components:
- A subscription to the Intel Provisioning Certification Service (Intel PCS), which provides you with the API keys needed to query the service for Intel SGX attestation collateral.
- A data center caching service, which acts as a caching proxy for the Intel PCS.
- An Intel SGX enabled platform, which must be provisioned before it can execute runtime Intel SGX workloads.
The goal of this guide is to produce a simplified, but not trivialized, environment with the following requirements:
- The caching service shall be run on a discreet system. Specifically, it shall not be a system that is used to run Intel SGX workloads.
- The system that hosts the caching service shall not require Intel SGX.
- The Intel SGX enabled platform shall be provisioned and then re-imaged with a fresh OS.
This guide will also assume that the Intel SGX enabled platform can be provisioned on a production network. This may not be a valid assumption in a data center’s production environment, but it removes unnecessary complexity from a development and testing setup.
Intel SGX DCAP Installation Procedure
At a high level, the steps to produce the minimum Intel SGX DCAP environment are:
- Subscribe to the Intel PCS for ECDSA Attestation and obtain the required API keys.
- Set up Intel's reference caching service, the Provisioning Certification Caching Service (PCCS).
- Provision the Intel SGX enabled platform for Intel SGX workloads.
- Verify the provisioning data.
- Reimage the Intel SGX enabled platform.
- Load the Intel SGX runtime stack onto the reimaged system.
The last two steps are intended to simulate real-world environments, where system provisioning might occur on a restricted network prior to deployment into production. They also ensure that the runtime system does not retain any of the provisioning components.
Subscribe to the Intel PCS
Each subscription to the Intel PCS Service for ECDSA Attestation issues two API keys: a primary key and a secondary key. Either one can be used. The point of issuing two keys is to provide continuity of service in the event the active key needs to be regenerated.
To subscribe to the service, browse to the Intel SGX Software Services page. If you have an account, sign in using the "Sign In" link in the banner. If you don't have an account, click "Sign Up" to register.
Once you are logged in, return the Intel SGX Software Services page. Under the "Intel Provisioning Certification Service for ECDSA Attestation" header, click on the link titled "Intel® SGX provisioning certification service".

From there, scroll down to the "Get PCK Certificate/s" API and click on the "Subscribe" button.

You'll be taken to a subscription summary page. Confirm your choices by clicking on the "Add subscription" button.

This will load a subscription summary page for your account. Scroll down to the "Intel® Software Guard Extensions Provisioning Certification Service subscription" section and click on the "Show" links to reveal your API keys.

Set up the Intel PCCS
Now that you have your API keys, you can set up the Intel PCCS as your caching service. The following steps assume you are starting from a fresh installation of Ubuntu Linux 20.04 LTS.
The PCCS package has a dependency on Node®.js version 14 which is not part of the 20.04 LTS distribution, so the first step is to fetch the Node.js setup script.
$ curl -o setup.sh -sL https://deb.nodesource.com/setup_14.x
$ chmod a+x setup.sh
$ sudo ./setup.sh
Once the script completes, you can add the Node.js package using apt.
$ sudo apt-get -y install nodejs
We'll use Intel's Debian packages for the Intel SGX DCAP installation, but to do that we need to add the repository to the list of sources for apt, and add the key:
$ sudo su
# echo 'deb [arch=amd64] https://download.01.org/intel-sgx/sgx_repo/ubuntu focal main' > /etc/apt/sources.list.d/intel-sgx.list
# wget -O - https://download.01.org/intel-sgx/sgx_repo/ubuntu/intel-sgx-deb.key | apt-key add -
# apt update
Now we're ready to install the prerequisite software. We'll use SQLite* as the database storage engine (this is the default setting for the PCCS). The PCCS will also need to compile a Node.js module for interfacing with C libraries, so we have to add the build-essential meta-package to the list.
# apt install sqlite3 python build-essential
Once that installation has finished, you can install the PCCS package.
# apt install sgx-dcap-pccs
The installation will run the PCCS setup script, which will ask you several questions.
Do you want to configure PCCS now? (Y/N)
Answer "Y" to this question.
Set HTTPS listening port [8081] (1024-65535)
Accept the default listening port of 8081, or select a non-privileged port number.
Set the PCCS service to accept local connections only? [Y] (Y/N)
Answer "N" to this question. We want the PCCS service to accept connections from other systems.
Set your Intel PCS API key (Press ENTER to skip)
Enter either your primary or secondary key.
Choose caching fill method : [LAZY] (LAZY/OFFLINE/REQ)
Answer "REQ" to this question. This places the caching service in the "on request" mode, which means it will fetch the attestation collateral for hosts as provisioning requests are received. For more information on the PCCS caching modes, see the white paper titled Design Guide for Intel® SGX Provisioning Certificate Caching Service (Intel® SGX PCCS) .
Next it will prompt you for an admin password and a user password. The admin password is used by the administration tool to manage the contents of the caching service's database. The user password is used by the provisioning tool. Create a password for each. Administration of the caching service is outside the scope of this guide.
Last, it will ask you if you want to generate a self-signed certificate for testing. Answer "Y" to this question, and then fill out the certificate request as you see fit. Remember that this is a self-signed certificate for testing and development purposes only. A production environment will require a certificate that is signed by a recognized certificate authority.
Verify the empty cache
We’ll inspect the contents of the PCCS collateral cache using the sqlitebrowser utility, which is a graphical application for working with SQLite databases. Install it using apt and then execute it on the command line, pointing it at the PCCS database:
$ sudo apt -y install sqlitebrowser
$ sqlitebrowser /opt/intel/sgx-dcap-pccs/pckcache.db
Use the “Browse Data” tab to examine the tables. They should all be empty.

Provisioning a system
Now that the PCCS is up and running, it’s time to provision an Intel SGX enabled platform. This guide assumes you have already enabled Intel SGX in the system BIOS, and imaged it with a fresh installation of Ubuntu Server 20.04 LTS.
Before we can install the Intel SGX driver, it’s necessary to add the Dynamic Kernel Module Support package:
$ sudo apt install dkms
Once that’s done, you can fetch the driver for Intel SGX DCAP and install it.
$ https://download.01.org/intel-sgx/sgx-dcap/1.9/linux/distro/ubuntu20.04-server/sgx_linux_x64_driver_1.36.2.bin
$ chmod 755 sgx_linux_x64_driver_1.36.2.bin
$ sudo ./sgx_linux_x64_driver_1.36.2.bin
Verify that the driver loaded by checking the kernel log:
$ dmesg | grep sgx
[ 245.139608] intel_sgx: loading out-of-tree module taints kernel.
[ 245.139702] intel_sgx: module verification failed: signature and/or required key missing - tainting kernel
[ 245.142415] intel_sgx: EPC section 0x2000c00000-0x207f7fffff
[ 245.154474] intel_sgx: EPC section 0x4000c00000-0x407fffffff
[ 245.167151] intel_sgx: Intel SGX DCAP Driver v1.36.2
The messages show that the driver successfully loaded and assigned memory to the Enclave Page Cache (EPC). You can ignore the warnings: they stem from the fact that this is an out-of-tree kernel driver.
Now we can install the provisioning tools. In a production environment, the provisioning binary and its supporting libraries might be incorporated into a minimal kernel image that is loaded via a PXE boot, but for testing purposes we’ll assume a production network and load the Intel SGX support packages directly from Intel’s repository.
The provisioning tool is distributed as a standalone package since it won’t typically be installed on a live system, but there is no release for Ubuntu 20.04 at the current time. Until one is ready, we'll need to install it using the Debian packages. This will also pull in a number of other dependencies that would not normally be present in a production provisioning image, but it's fine for testing purposes:
$ echo 'deb [arch=amd64] https://download.01.org/intel-sgx/sgx_repo/ubuntu focal main' | sudo tee /etc/apt/sources.list.d/intel-sgx.list > /dev/null
$ wget -O - https://download.01.org/intel-sgx/sgx_repo/ubuntu/intel-sgx-deb.key | sudo apt-key add -
$ sudo apt update
$ sudo apt install sgx-pck-id-retrieval-tool
Now the provisioning tool needs to be configured so that it knows how to contact the caching service. Edit the configuration file /opt/intel/sgx-pck-id-retrieval-tool/network_setting.conf and make the following changes:
- Change the PCCS_URL to match your caching service’s location.
- Uncomment the user_token parameter, and set it to the user password you created when configuring the PCCS
- Set the proxy_type to fit your environment (most likely this will be “direct”)
- Ensure USE_SECURE_CERT is set to “FALSE” since we’re using a self-signed certificate for testing purposes. In a production environment, this should be set to “TRUE”.
Save your changes and run the provisioning tool:
$ PCKIDRetrievalTool
Intel(R) Software Guard Extensions PCK Cert ID Retrieval Tool Version 1.9.100.3
ERROR: readUEFIVar: failed to open uefi variable /sys/firmware/efi/efivars/SgxRegistrationServerRequest-304e0796-d515-4698-ac6e-e76cb1a71c28 ,error: No such file or directory
ERROR: getRequestType: SgxRegistrationServerRequest UEFI variable was not found.
Warning: platform manifest is not available or current platform is not multi-package platform.
Warning: Couldn't collect platform manifest. If you are using single-package platform, you can ignore this warning.
the data has been sent to the cache service successfully and pckid_retrieval.csv has been generated successfully!
When running on a single socket system you can ignore the warnings about the platform manifest and the UEFI variable for the Registration Server. The last line is the most important as it tells us the system has been successfully provisioned.
Verify the provisioned system
We can verify the provisioning by returning to the SQLite database using sqlitebrowser. There should be data present in every table. The screen shot below shows the contents of the table fmspc_tcbs. Note the tcbinfo data structure on the right.

Runtime configuration
Now that the Intel SGX enabled platform has been provisioned, it can be loaded with a production OS image. It can, in fact, be reimaged multiple times: as long as the Intel SGX Trusted Compute Base (TCB) doesn’t change, it will not need to be reprovisioned.
Again, we’ll assume a fresh install of Ubuntu Server 20.04 LTS as the starting point. Install the driver:
$ sudo apt install dkms
$ wget https://download.01.org/intel-sgx/sgx-dcap/1.9/linux/distro/ubuntu20.04-server/sgx_linux_x64_driver_1.36.2.bin
$ chmod 755 ./sgx_linux_x64_driver_1.36.2.bin
$ sudo ./sgx_linux_x64_driver_1.36.2.bin
Update the apt repositories:
$ echo 'deb [arch=amd64] https://download.01.org/intel-sgx/sgx_repo/ubuntu focal main' | sudo tee /etc/apt/sources.list.d/intel-sgx.list > /dev/null
$ wget -O - https://download.01.org/intel-sgx/sgx_repo/ubuntu/intel-sgx-deb.key | sudo apt-key add -
$ sudo apt update
Now you can install the Intel SGX runtime components, and Intel’s reference quoting library and quote provider library.
$ sudo apt-get install libsgx-urts libsgx-dcap-ql libsgx-dcap-default-qpl
This step will also install Intel’s Architectural Enclave Service Manager which needs to be configured for ECDSA-based attestations. Edit the configuration file, /etc/aesmd.conf, and uncomment this line:
default quoting type = ecdsa_256
Since we’re using ECDSA quotes, AESM has no need to connect to the internet and you can leave the proxy settings alone.
Restart AESM for the changes to take effect:
$ systemctl restart aesmd
Next, we need to configure the quote provider library to connect to PCCS to obtain the attestation collateral. Edit the configuration file, /etc/sgx_default_qcnl.conf, and make the following changes:
- Set the PCCS_URL parameter to the location of our PCCS server
- Set USE_SECURE_CERT to “FALSE” since we’re using a self-signed certificate for testing purposes. Again, in a production environment, this should be set to “TRUE”.
This system is now ready to run Intel SGX workloads.
§