Intel® Unique Platform ID Overview
The Intel® Unique Platform ID (Intel® UPID) is a globally unique and persistent identity that can be used to identify a platform throughout its lifecycle. The Intel UPID is equipped with an IDevID (Initial Device Identifier) private key that is protected by the Intel® CSME security engine and an IDevID certificate issued by the Intel certificate authority. The certificate adheres to the IEEE 802_1AR 2018 industry standard for IDevID certificates.
The Intel UPID can be used to challenge (and verify) a client endpoint’s identity for various purposes. The Intel UPID IDevID certificate is issued by the Intel® CSME On Die Certificate Authority (Intel® ODCA) infrastructure. The Intel CSME Firmware UPID application provides a host API that allows an application with admin level privileges in the OS or BIOS to challenge the Intel® CSME firmware to obtain a signed proof of the identity of the PC on which the application is executing.
This Intel UPID guide can assist application developers in incorporating use of the Intel UPID attestation in their applications.
Intel UPID Advantages
- The Intel UPID does not change, and cannot be changed, throughout the device lifecycle.
- The Intel UPID cannot be spoofed. Its integrity is protected, and it cannot be overwritten.
- The Intel UPID can be updated when a platform is refurbished.
- The Intel UPID is attestable by the Intel CSME.
Privacy Controls
The following features are included to satisfy privacy concerns:
- The user application interface requires OS administrator privileges to access the Intel CSME API that returns the Intel UPID, its IDevID certificate, and the certificate chain, and to access the Intel UPID Attestation API.
- An Intel CSME API is provided to allow the BIOS to control OS access to the Intel UPID APIs.
- The Intel UPID feature state controls access to the Intel UPID APIs. When the Intel UPID feature state is disabled, access to Intel UPID APIs that read the UPID or attest the UPID is blocked.
Intel UPID Usage Examples
Following are some examples of uses for the Intel UPID IDevID:
- Verifying a device’s identity when it is returned by the customer. The UPID_PLATFORM_ID_GET command can be used to read the device’s Intel UPID in the factory before the device is shipped. When a customer returns the device for servicing, or when a customer attempts to access a service specific to the device, the same APIs can be used to verify that the same device is being returned or is accessing the service.
- Using the Intel UPID when onboarding a device. The OEM can deliver a list of the device Intel UPIDs to the purchaser of the devices (for example, to an IT department that has purchased many devices). The purchaser can then use this list when an end-user attempts to onboard the device, to ensure that the device being onboarded is indeed the same one that the customer ordered.
- Disabling Intel UPID when it is not needed, to prevent unauthorized tracking of the device by OS-level applications. The OEM can implement a mechanism in the BIOS to prevent the OS from enabling the Intel UPID. The BIOS must enable reading Intel UPID to allow the OS to read it. If the BIOS has not disabled the Intel UPID, software with OS admin privileges can use the UPID_PLATFORM_ID_FEATURE_STATE_SET command to enable it and can read it. It is recommended for the OS to disable Intel UPID (by using the same command UPID_PLATFORM_ID_FEATURE_STATE_SET), so that if in the future the level of privilege needed to read Intel UPID differs from the level required to enable it, the customer has the option of disabling so that applications without Administrator privileges cannot access it.
- Attesting the device’s Identity as an additional factor for zero-trust access to corporate services and resources. The enterprise can collect the Intel UPIDs of the devices that it owns and can map each Intel UPID to the employee using the device. When a user attempts to access a corporate service or resource, the policy can ensure that the user can access it only from their approved device. To attest the device’s identity, the UPID_OEM_PLATFORM_ID_SIGN command is invoked.
System Requirements
Intel UPID is supported on 11th Generation (Tiger Lake) Intel vPro® or Intel vPro® Essentials devices and later programs.
The availability of the Intel UPID feature depends on the OEM enabling the support in the platform hence it may not be available for all platforms of these generations.
(See Detecting Whether Intel UPID is Supported on the Platform.)
The following table lists the programs that support Intel UPID, and the Intel CSME versions that also support device attestation:
| Platform | InteI CSME Firmware Versions Supporting Device Attestation |
|---|---|
| Tiger Lake | 15.0.42.X and later |
| Eagle Stream | 15.20.5.X and later |
| Alder Lake | 16.1.25.X and later |
| Fish Hawk Falls | 16.10.5.X and later |
| Raptor Lake and later | All |
Intel UPID Structure
Following is the structure of the Intel UPID:

|
Field
|
Description
|
Comments
|
||||||||||||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| OEM Platform ID | 32 bytes. Can optionally be set by the OEM BIOS before End of Manufacturing |
Stored in Non-Volatile Memory protected by Intel CSME | ||||||||||||||||||||||||||||||||||
| Truncated SHA256 | Truncated SHA256 of Intel CSME ROM On-Die-CA certificate provisioned to the Intel CSME fuses at Intel factory |
|||||||||||||||||||||||||||||||||||
| RSVRD | ||||||||||||||||||||||||||||||||||||
| OEM Platform ID Refurbish Counter | Can be incremented by the OEM BIOS when the device is refurbished. Stored in Intel CSME FPFs |
|||||||||||||||||||||||||||||||||||
| HW Generation | Initialized by the Intel CSME firmware |
Identifies the platform generation. Read from
|
||||||||||||||||||||||||||||||||||
|
OEM ID |
The vendor ID allocated by PCI-SIG |
Set by the manufacturer in the Intel CSME |
Intel CSME On Die CA
During Intel manufacturing, the Intel chipset is provisioned with a Certificate Authority certificate issued by the Intel Key Generation Facility (iKGF). This enables an on-die CA (Intel® ODCA) on the Intel platform to issue certificates for individual Intel CSME applications. The Intel ODCA issues the Intel UPID certificate, enabling Intel UPID Attestation. The Intel UPID certificate is issued following IEEE 802.1AR for an IDevID (initial device identity) certificate.
The following diagrams describe the Intel ODCA infrastructure in the Intel CSME firmware on different platforms.
When Intel UPID is enabled, the certificate includes the Intel UPID in alignment with the 802.1AR defined IDevID Certificate.
The ODCA TLS-Server certificate is used for the provisioning flow.
Certificate Chain for Tiger Lake and Alder Lake Platforms:
Certificate Chain for Raptor Lake and Lunar Lake Platforms:
* Starting from Meteor Lake, the chain no longer includes the PAVP CA certificate.
Certificate Chain for Panther Lake Platforms:
The Intel CSME application key generation includes the following:
- the Intel CSME application’s Security Version Number (SVN)
- the application’s module ID
The Intel CSME certificate is revoked by Intel iKGF when the application’s SVN is incremented. Intel iKGF publishes the revoked certificates in a CRL (Certificate Revocation List).
Intel UPID IDevID Certificate Attributes
The platform uses the IDevID certificate to attest Intel UPID.
For definitions of the UPID OEM_ID, OEM Platform ID and CSME HW ID, see the table in Intel® UPID Structure above.
The certificate complies with the IEEE 802.1AR IDevID 2018 certificate standard and includes the following attributes:
|
Field
|
Value
|
|
|---|---|---|
|
Subject |
X520SerialNumber (OID = 2.5.4.5): |
< OEM Platform ID > in Hex char string format. Stored in protected Intel CSME non-volatile memory |
|
X520OrganizationName (OID = 2.5.4.10) |
<OEM_ID> OEM PCIe Vendor ID in Intel CSME fuses |
|
|
CommonName |
For Intel UPID Certificate: ” CSME IDevID OS /BIOS” |
|
|
subjectAltName (RFC4108) |
(OID = 1.3.6.1.5.5.7.8.4) HardwareModuleName ::= SEQUENCE { hwType OBJECT IDENTIFIER hwSerialNum OCTET STRING } |
hwType OBJECT IDENTIFIER: 2.16.840.1.113741.1.5.3.6.1 indicates that this is an Intel CSME UPID ODCA Hardware ID hwSerialNum OCTET STRING = the “<CSME HW ID>” |
|
Extended Key Usage |
X.509 V3 Extension |
2.16.840.1.113741.1.2.4.6 – for BIOS Intel UPID attestation 2.16.840.1.113741.1.2.4.7 – for OS Intel UPID attestation |
| Intel Brand Identity Extension | X.509 V3 Extension |
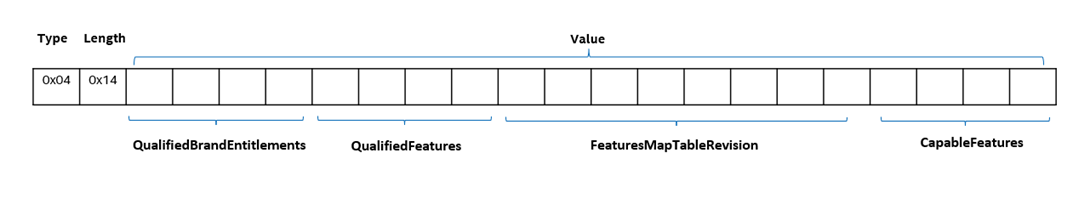
2.16.840.1.113741.1.2.5.1 Structure:
Qualified Brand and Entitlements: 4 bytes. Each bit represents a different entitlement. A value of 1 indicates that the entitlement is included. Field structure: Bit 0: Intel® Connectivity Performance Suite Bit 1: Intel vPro® Enterprise Brand Bit 2: Intel vPro® Essentials Brand Bit 3: Reserved Bit 4: Intel® Based PC Brand / For workstation: Intel® Xeon® Based Workstation (when Brand Features Map Table Revision is 19.10.x.x) Bits 5-30: Reserved Bit 31: Intel® Connection Manager Entitlement
Intel CSME Brand Qualified Features: 4 bytes. Each bit represents a different Intel CSME feature. A value of 1 indicates that the feature is qualified. Note: Some features are mandatory - they must be enabled by the OEM. Other features are optional. Whether a feature is mandatory or optional depends on the platform. To discover which features are mandatory and which are optional for your platform, refer to the Intel® Unique Platform ID landing page. Bit 0: Intel® AMT Bit 1: Intel® Standard Manageability Bit 2: Reserved Bit 3: Intel® One-Click Recovery Bit 4: Intel® Remote Platform Erase Bit 5: Intel® Platform Service Record Bits 6-17: Reserved Bit 18: Out of Band KVM Remote Control Bits 19-23: Reserved Bit 24: Intel® Trusted Endpoint Provisioning (Intel TEP) Bits 25-26: Reserved Bit 27: Out of Band Over ThunderboltTM Dock Bit 28: Intel® Unique Platform ID Bit 29-31: Reserved
Brand Features Map Table Revision: 8 bytes Bytes 0-1: Major version of Intel CSME firmware Bytes 2-3: Minor version of Intel CSME firmware Bytes 4-5: Hot fix number of Intel CSME firmware Bytes 6-7: Build number (version of the map table – across generations)
CPU Brand Qualified Features: 4 bytes. Each bit represents a different CPU feature. A value of 1 indicates that the feature is qualified. Bit 0: Intel® System Security Report Bit 1: Intel® Runtime BIOS Resilience L2 Bit 2: Intel® System Resources Defense Bit 3: NVMe Based Firmware Recovery Bit 4: Intel® Security Report Bits 5-9: Reserved Bit 10: Intel Connectivity Performance Suite Bits 11-15: Reserved Bit 16: Intel® Trusted Execution Technology Bit 17: Intel® VT-rp Bit 18: Intel® Total Memory Encryption – Multi Key Bit 19: Intel® Total Storage Encryption Bit 20: Intel® Trusted Domain Extensions Bits 21-31: Reserved
Extension: = SEQUENCE {2 elm OBJECT IDENTIFIER 2.16.840.1.113741.1.2.5.1, OCTET STRING OCTET STRING [Qualified Brand and Entitlements || CSME Brand QualifiedFeatures || Brand Features Map Table Revision || CPU Brand Qualified Features] } where || stands for concatenation of the values above. |
Intel UPID MEI Commands
Intel UPID MEI Client Definition
GUID = 92136C79-5FEA-4CFD-980E-23BE07FA5E9F
TxBufferSize = 1200 bytes
RxBufferSize = 3,500 bytes
MaxClients = 1
Detecting Whether Intel UPID is Supported on the Platform
A platform’s Intel UPID capability can be detected from the presence of the Intel UPID MEI client in the Intel CSME firmware. When the Intel UPID MEI client is present, it registers its GUID with the Intel MEI driver.
The Intel MEI driver provides an interface through which software can query the list of HECI Client GUIDs supported by the Intel CSME firmware and thereby discover whether the Intel UPID MEI Client GUID is on the list. Once the Intel UPID MEI Client GUID has been found, it is also possible to discover the version of the Intel UPID feature.
If Intel UPID is not supported on the platform, the OEM should be contacted to enable the feature.
To query the Intel MEI driver for the supported Intel MEI Client GUIDs and GUID versions:
- Use the GetDevicePath function to retrieve the Intel MEI driver filename via GUID.
- Open a handle to the Intel MEI driver (via CreateFile, using the filename discovered in Step 1).
- To discover the number of supported GUIDs:
- Send IOCTL - IOCTL_TEEDRIVER_GET_FW_CLIENT_COUNT (via DeviceIoControl())
- Input buffer – None
- Output Buffer – FW_CLIENT_COUNT struct
- Send IOCTL - IOCTL_TEEDRIVER_GET_FW_CLIENT_COUNT (via DeviceIoControl())
- Send a query that will return a list of structures that describes each one of the supported Intel MEI GUIDs. The number of entries in the structure equals the FW_CLIENT_COUNT extracted in Step 3:
- Send IOCTL - IOCTL_TEEDRIVER_GET_FW_CLIENTS (via DeviceIoControl())
- Input Buffer – None
- Output Buffer – Array of FW_CLIENT_EXPANDED structure. The number of entries is equal to FW_CLIENT_COUNT (see the FW_CLIENT_EXPANDED definition).
- Send IOCTL - IOCTL_TEEDRIVER_GET_FW_CLIENTS (via DeviceIoControl())
- For each entry, compare FW_CLIENT_EXPANDED.ProtocolName with the Intel UPID MEI Client GUID (92136C79-5FEA-4CFD-980E-23BE07FA5E9F). If found, the Intel UPID feature is supported.
- In the Intel UPID FW_CLIENT_EXPANDED structure found in Step 5, check the FW_CLIENT_EXPANDED.ProtocolVersion to determine the version of the Intel UPID protocol that the firmware supports.
Definitions:
typedef struct _FW_CLIENT_EXPANDED
{
UINT16 ClientID; // FW Client Number
GUID ProtocolName; // FW Client GUID
UINT8 ProtocolVersion; // FW Client Protocol Version
UINT8 MaxNumberOfConnections;
UINT8 FixedAddress;
UINT8 SingleReceiveBuffer;
UINT32 MaxMessageLength; // FW Max Buffer Size
} FW_CLIENT_EXPANDED;
typedef struct _FW_CLIENT_COUNT
{
BYTE count;
} FW_CLIENT_COUNT;
#define IOCTL_TEEDRIVER_GET_FW_CLIENT_COUNT \
CTL_CODE(FILE_DEVICE_HECI, 0x806, METHOD_BUFFERED, FILE_READ_ACCESS | FILE_WRITE_ACCESS)
#define IOCTL_TEEDRIVER_GET_FW_CLIENTS \
CTL_CODE(FILE_DEVICE_HECI, 0x807, METHOD_BUFFERED, FILE_READ_ACCESS | FILE_WRITE_ACCESS)
UPID MEI Command Structure
UPID_HECI_HEADER
Header for Intel UPID commands.
typedef struct
{
UINT8 Feature;
UINT8 Command;
UINT16 ByteCount;
} UPID_HECI_HEADER;
Field Description
| Field Name | Field Type | Description |
|---|---|---|
|
Feature |
UINT8 |
The command feature code. See UPID_COMMAND_FEATURE for feature codes. |
|
Command |
UINT8 |
The command code. See UPID_COMMAND for command codes. |
|
ByteCount |
UINT16 |
Total length, excluding the message header. |
UPID_COMMAND_FEATURE
Command feature codes.
typedef enum
{
UPID_COMMAND_FEATURE_PLATFORM_ID = 0,
UPID_COMMAND_FEATURES_TEP = 1,
} UPID_COMMAND_FEATURE;
Note: sizeof(enum) is sizeof(UINT32) = 4 bytes.
UPID_COMMAND
Command codes for the Platform ID feature (0).
typedef enum
{
UPID_PLATFORM_ID_SUPPORT_GET_CMD = 0,
UPID_PLATFORM_ID_STATE_GET_CMD = 1,
UPID_PLATFORM_ID_STATE_SET_CMD = 2,
UPID_PLATFORM_ID_OS_CONTROL_GET_CMD = 3,
UPID_PLATFORM_ID_OS_CONTROL_SET_CMD = 4,
UPID_PLATFORM_ID_GET_CMD = 5,
UPID_PLATFORM_ID_REFURBISH_COUNTER_GET_CMD = 6,
UPID_OEM_PLATFORM_ID_UPDATE_CMD = 7,
} UPID_PLATFORM_ID_FEATURE_COMMANDS;
Note: sizeof(enum) is sizeof(UINT32) = 4 bytes.
UPID_STATUS
Status codes.
typedef enum
{
UPID_STATUS_SUCCESS = 0,
UPID_STATUS_FEATURE_NOT_SUPPORTED = 1,
UPID_STATUS_INVALID_INPUT_PARAMETER = 2,
UPID_STATUS_STATUS_INTERNAL_ERROR = 3,
UPID_STATUS_NOT_ALLOWED_AFTER_EOP = 4,
UPID_STATUS_NOT_ALLOWED_AFTER_MANUF_LOCK = 5,
UPID_STATUS_MAX_COUNTERS_EXCEEDED = 6,
UPID_STATUS_INVALID_STATE = 7,
UPID_STATUS_RESERVED2 = 8,
UPID_STATUS_NOT_ALLOWED_AFTER_CBD = 9,
} UPID_STATUS;
Note: sizeof(enum) is sizeof(UINT32) = 4 bytes.
| Status | Caused By (in Specific Command) |
|---|---|
| UPID_STATUS_FEATURE_NOT_SUPPORTED (Invalid command code) |
|
| UPID_STATUS_INVALID_INPUT_PARAMETER (Input size does not match the expected request size for the specific command) |
UPID_HECI_OEM_PLATFORM_ID_UPDATE
UPID_HECI_OEM_PLATFORM_ID_SIGN
UPID_HECI_OEM_PLATFORM_ID_GET_CERTIFICATE_CHAIN:
|
| UPID_STATUS_INTERNAL_ERROR (Examples: file system error, crypto error) |
|
| UPID_STATUS_NOT_ALLOWED_AFTER_EOP |
UPID_HECI_PLATFORM_ID_FEATURE_STATE_SET
UPID_HECI_PLATFORM_ID_FEATURE_STATE_OS_CONTROL_SET
UPID_HECI_OEM_PLATFORM_ID_UPDATE
UPID_HECI_OEM_PLATFORM_ID_SIGN:
|
| UPID_STATUS_INVALID_STATE |
UPID_HECI_PLATFORM_ID_GET
|
|
UPID_STATUS_NOT_ALLOWED_AFTER_ |
UPID_HECI_OEM_PLATFORM_ID_UPDATE
|
| UPID_STATUS_MAX_COUNTER_EXCEEDED |
UPID_HECI_OEM_PLATFORM_ID_UPDATE
|
| UPID_STATUS_INVALID_STATE |
UPID_HECI_OEM_PLATFORM_ID_SIGN
UPID_HECI_OEM_PLATFORM_ID_GET_CERTIFICATE_CHAIN:
UPID_HECI_PLATFORM_ID_GET
|
| UPID_STATUS_NOT_ALLOWED_AFTER_CBD |
UPID_HECI_OEM_PLATFORM_ID_UPDATE
|
UPID_PLATFORM_ID_FEATURE_SUPPORT_GET
Returns the UPID feature support.
UPID_PLATFORM_ID_FEATURE_SUPPORT_GET Request
typedef struct
{
UPID_HECI_HEADER Header;
} UPID_PLATFORM_ID_FEATURE_SUPPORT_GET_Request;
| Field Name | Field Type | Description |
|---|---|---|
| Header | UPID_HECI_HEADER | Request header |
UPID_PLATFORM_ID_FEATURE_SUPPORT_GET Response
typedef struct
{
UPID_HECI_HEADER Header;
UPID_STATUS Status;
PlatformIdSupported platformIdSupported;
} UPID_PLATFORM_ID_FEATURE_SUPPORT_GET_Response;
|
Field Name
|
Field Type
|
Description
|
|---|---|---|
|
Header |
Response header |
|
|
Status |
Status |
|
|
platformIdSupported |
UPID_SUPPORT |
UPID and Attestation support state |
PlatformIdSupported
typedef union _UPID_SUPPORT {
UINT8 PlatformIdSupported;
Struct {
UINT8 Supported: 1;
//0: UPID not supported
//1: supported
UINT8 Attestation: 1;
//0: UPID Attestation not supported
//1: supported
UINT8 Reserved:6
}
} UPID_SUPPORT;
Note: If a platform supports Intel UPID Attestation, the value of PlatformIdSupported is 3 (i.e., Intel UPID must also be supported on the platform).
UPID_PLATFORM_ID_FEATURE_STATE_GET
Returns the Platform ID feature state.
UPID_PLATFORM_ID_FEATURE_STATE_GET Request
typedef struct
{
UPID_HECI_HEADER Header;
} UPID_PLATFORM_ID_FEATURE_STATE_GET_Request;
|
Field Name
|
Field Value
|
Description
|
|---|---|---|
|
Header |
Request header |
UPID_PLATFORM_ID_FEATURE_STATE_GET Response
typedef struct
{
UPID_HECI_HEADER Header;
UPID_STATUS Status;
UINT8 FeatureEnabled;
} UPID_PLATFORM_ID_FEATURE_STATE_GET_Response;
|
Field Name
|
Field Value
|
Description
|
|---|---|---|
|
Header |
Response header |
|
| Status | UPID_STATUS | Status |
| FeatureEnabled | UINT8 | Feature state (0/1) |
UPID_PLATFORM_ID_FEATURE_STATE_SET
Sets the Platform ID feature state.
UPID_PLATFORM_ID_FEATURE_STATE_SET Request
typedef struct
{
UPID_HECI_HEADER Header;
UINT8 FeatureEnabled;
} UPID_PLATFORM_ID_FEATURE_STATE_SET_Request;
|
Field Name
|
Field Value
|
Description
|
|---|---|---|
|
Header |
Request header |
|
|
FeatureEnabled |
UINT8 |
Feature state (0/1) |
UPID_PLATFORM_ID_FEATURE_STATE_SET Response
typedef struct
{
UPID_HECI_HEADER Header;
UPID_STATUS Status;
} UPID_PLATFORM_ID_FEATURE_STATE_SET_Response;
|
Field Name
|
Field Value
|
Description
|
|---|---|---|
|
Header |
Response header |
|
|
Status |
Status |
UPID_PLATFORM_ID_GET
Returns the Unique Platform ID of the system.
UPID_PLATFORM_ID_GET Request
typedef struct
{
UPID_HECI_HEADER Header;
} UPID_PLATFORM_ID_GET_Request;
| Field Name | Value | Description |
|---|---|---|
| Header | UPID_HECI_HEADER | Request header |
UPID_PLATFORM_ID_GET Response
typedef struct
{
UPID_HECI_HEADER Header;
UPID_STATUS Status;
UPID_OEM_PLATFORM_ID_TYPE PlatformIdType;
UINT8[32] OEMPlatformId;
UINT8[32] CSMEPlatformId;
} UPID_PLATFORM_ID_GET_Response;
| Field Name | Value | Description |
|---|---|---|
|
Header |
UPID_HECI_HEADER |
Response header |
|
Status |
UPID_STATUS |
Status |
|
PlatformIdType |
OEM Platform ID type |
|
|
OEMPlatformId |
UINT8[32] |
OEM Platform ID |
|
CSMEPlatformId |
UINT8[32] |
Intel CSME Platform ID |
Note: After retrieving the UPID, it is recommended to disable the feature state using UPID_PLATFORM_ID_FEATURE_STATE_SET.
UPID_OEM_PLATFORM_ID_TYPE
UPID presentation type.
typedef enum
{
UPID_OEM_PLATFORM_ID_TYPE_NOT_SET = 0,
UPID_OEM_PLATFORM_ID_TYPE_BINARY = 1,
UPID_OEM_PLATFORM_ID_TYPE_PRINTABLE_STRING = 2,
} UPID_OEM_PLATFORM_ID_TYPE;
Note: sizeof(enum) is sizeof(UINT32) = 4 bytes.
| Item Name | Description |
|---|---|
| UPID_OEM_PLATFORM_ID_TYPE_NOT_SET | OEM Platform ID is not set. |
| UPID_OEM_PLATFORM_ID_TYPE_BINARY | OEM Platform ID includes binary values. |
| UPID_OEM_PLATFORM_ID_TYPE_PRINTABLE_STRING | OEM Platform ID includes printable characters. |
UPID_PLATFORM_ID_SIGN
Signs user data with device key.
UPID_OEM_PLATFORM_ID_SIGN Request
typedef struct
{
UPID_HECI_HEADER Header
UPID_KEY_IDX KeyIdx
UINT32 DataLen//actual length of data in the dataToSign buffer
UINT8[DATA_TO_SIGN_MAX_SIZE] DataToSign;
} UPID_PLATFORM_ID_SIGN_Request;
UPID_KEY_IDX
Private key used for signing. Specifies the type of key requested from the firmware, depending on whether
the signing request is coming from an OS application (1) or from the BIOS (0).
typedef enum
{
UPID_KEY_IDX_BIOS = 0,
UPID_KEY_IDX_OS = 1,
} UPID_KEY_IDX;
Note: sizeof(enum) is sizeof(UINT32) = 4 bytes.
| Field Name | Description |
|---|---|
| KeyIdx |
User key type: 0: BIOS 1: OS |
| DataLen | Actual length of data in the dataToSign buffer |
| DataToSign |
The data that is signed by the Intel CSME key using the ECDSA384_WITH_SHA384 algorithm. DATA_TO_SIGN_MAX_SIZE is 1024 bytes. |
UPID_OEM_PLATFORM_ID_SIGN Response
typedef struct
{
UPID_HECI_HEADER Header
STATUS Status
SIGNATURE_MECHANISM SignatureMechanism
UINT8[512] Signature
} ECDSADeviceSignChallenge_Response;
| Field Name | Description |
|---|---|
| SignatureMechanism |
Signature mechanism used. 0 – ECDSA 384 SHA384 |
| Signature |
Signature over the input "dataToSign". Note: Actual signature size may be smaller than the signature buffer and depends on the algorithm used in SignatureMechanism |
UPID_OEM_PLATFORM_ID_GET_CERTIFICATE_CHAIN
Get the On Die CA certificate chain used for signing user data.
UPID_OEM_PLATFORM_ID_GET_CERTIFICATE_CHAIN Request
typedef struct
{
UPID_HECI_HEADER Header;
UINT32 CertIdx
} GetCertificateChain_Request;
| Field name | Description |
|---|---|
| CertIdx | User certificate type. Specifies the type of certificate requested from the firmware, depending on whether the signing request is coming from an OS application (1) or from the BIOS (0). |
typedef enum
{
UPID_CERT_IDX_BIOS = 0,
UPID_CERT_IDX_OS = 1,
} UPID_CERT_IDX;
Note: sizeof(enum) is sizeof(UINT32) = 4 bytes.
UPID_OEM_PLATFORM_ID_GET_CERTIFICATE_CHAIN Response
typedef struct
{
UPID_HECI_HEADER Header;
STATUS Status
UINT16[4] LengthsOfCertificates;
UINT8[MAX_Certs_length] CertificateChain; //
} GetCertificateChain_Response;
| Field name | Description |
|---|---|
| LengthsOfCertificates | This field corresponds to the length of each one of the certificates returned by Certificates field. It returns 4 unit16, each one is the length of corresponding certificate in Certificates |
| CertificateChain |
This is the certificate chain to return in the order from leaf to root. E.g., the first certificate is the MAX_Certs_length is 3200. |
UPID_TEP_COMMAND
Command codes for the UPID TEP feature (1).
typedef enum
{
TEP_GET_TIME_SYNC_NONCE_CMD = 1,
TEP_SET_TIME_CERTS_CMD = 2,
TEP_OWNERSHIP_VOUCHER_REQUEST_CMD = 3,
TEP_SET_OWNERSHIP_CMD = 4,
TEP_GET_VOUCHERS_CMD = 5,
TEP_GET_OWNERSHIP_STATE_CMDD = 6,
TEP_OWNERSHIP_VOUCHER_UPDATE_REQUEST_CMD = 7,
TEP_OWNERSHIP_REMOVE_CMD = 8,
TEP_GET_CAPABILITIES_CMD = 9,
} UPID_TEP_PLATFORM_ID_FEATURE_COMMANDS;
Note: sizeof(enum) is sizeof(UINT32) = 4 bytes.
UPID_TEP_STATUS
Status codes.
typedef enum
{
TEP_SUCCESS = 0,
TEP_TIME_NOT_SET = 1,
TEP_INVALID_PARAMETER = 2,
TEP_NOT_ALLOWED = 3,
TEP_BAD_SIGNATURE = 4,
TEP_INVALID_NONCE = 5,
TEP_INTERNAL_ERROR = 6,
TEP_INVALID_CERT = 7,
TEP_INVALID_VOUCHER = 8,
TEP_OEM_ID_MISSMATCH = 9,
TEP_FEATURE_NOT_ALLOWED = 10,
TEP_INVALID_CMS = 11,
} UPID_TEP_STATUS;
Note: sizeof(enum) is sizeof(UINT32) = 4 bytes.
TEP_GET_CAPABILITIES_CMD
Returns the Intel TEP capabilities of the system.
TEP_GET_CAPABILITIES_CMD Request
typedef struct
{
UPID_HECI_HEADER Header;
} TEP_GET_CAPABILITIES_CMD_Request;
| Field Name | Value | Description |
|---|---|---|
| Header | UPID_HECI_HEADER | Request header |
TEP_GET_CAPABILITIES_CMD Response
typedef struct
{
UPID_HECI_HEADER Header;
STATUS Status;
UINT8 num_features;
UINT8[32] OEMPlatformId;
UINT8[TEP_MAX_FEATURES] features_list;
} TEP_GET_CAPABILITIES_CMD_Response;
| Field Name | Value | Description |
|---|---|---|
|
Header |
UPID_HECI_HEADER |
Response header |
|
Status |
STATUS |
TEP_STATUS values enum |
| max_vouchers | UINT8 | Maximum number of ownership vouchers supported. Note: In Panther Lake one voucher is supported. |
| num_features | UINT[8] | Number of features supported. Note: In Panther Lake one feature is supported. |
| features_list |
UINT8[TEP_MAX_FEATURES]] |
List of supported features identified by TEP_FEATURES. Note: Only Intel® AMT in Panther Lake. |
TEP_STATUS Values Returned:
| Status | Description |
|---|---|
| TEP_SUCCESS | All Good |
TEP_GET_TIME_SYNC_NONCE_CMD
Intel® TEP agent running on the OS of the endpoint being provisioned sends Intel® CSME a request ID (req_id) received from the Ownership Service. The request ID serves as a nonce.
Intel® CSME returns a random Intel CSME nonce along with an Intel® CSME signature over the returned data, including the request ID and CSME nonce.
TEP_GET_TIME_SYNC_NONCE_CMD Request
typedef struct{ UPID_HECI_HEADER Header; UINT8[20] req_id;} TEP_GET_TIME_SYNC_NONCE_CMD_Request;
| Field Name | Value | Description |
|---|---|---|
| Header | UPID_HECI_HEADER | Request header |
| req_id | UINT8[20] | Server-generated random request ID for server to verify the freshness of the Intel® CSME response |
TEP_GET_TIME_SYNC_NONCE_CMD Response
typedef struct{ UPID_HECI_HEADER Status; UINT8[20] req_id;UINT8[20] csme_nonce;CSME_SIGNATURE signature; } TEP_GET_TIME_SYNC_NONCE_CMD_Response;
| Field Name | Value | Description |
|---|---|---|
|
Header |
Response header |
|
|
Status |
STATUS |
TEP_STATUS values enum |
| req_id | UINT8[20] | Server-generated nonce |
| csme_nonce | UINT8[20] | Nonce (to be signed by Intel® CAaaS OCSP responder). The nonce is valid for 10 minutes. While the nonce is valid, Intel® CSME returns the same nonce if the API is invoked again. |
| signature | CSME_SIGNATURE | Signature over the response data signed with the CSME TEP ODCA certificate. Data included in the Signature: status + Req_id + csme_nonce + CSME_SIGNATURE.timestamp + CSME_SIGNATURE.signature_mechanism |
CSME_SIGNATURE
| Parameter Name | Parameter Type | Description |
|---|---|---|
| time_stamp | UINT32 | UTC time when data was signed. Included in the signature |
| signature_mechanism | UINT32 | This is a CSME enum. Always ECDSA384 for Panther Lake.Included in the signature |
| signature | UINT8[512] | Actual signature length determined by Signature Mechanism |
| certificates | UINT8[6000] | The certificate chain, certificates concatenated one after another, starting with the leaf certificate |
TEP_STATUS Values Returned
| TEP_SUCCESS | All good |
| TEP_INVALID_PARAMETER | |
| Status | Description |
|---|---|
| TEP_SUCCESS | All good |
| TEP_INVALID_PARAMETER | Length in UPID_HECI_HEADER is not equal to the size of the request structure |
| TEP_INTERNAL_ERROR |
An internal CSME firmware error |
TEP_SET_TIME_CERTS_CMD
Intel® TEP agent running on the OS of the endpoint being provisioned sends Intel® CSME an ownership voucher request. The request contains data that the ownership service wants to include in the voucher.
TEP_SET_TIME_CERTS Request
typedef struct
{
UPID_HECI_HEADER Header;
UINT16[4] length_of_certificates;
UINT8[60000] certificates;
UNT16[4] length_of_ocsp_response;
UINT8[6000] ocsp_response;
} TEP_SET_TIME_CERTS_CMD_Request;
| Field Name | Value | Description |
|---|---|---|
| Header | UPID_HECI_HEADER | Request header |
| length_of_certificates | UINT16[4] | Length of each certificate in Ownership Service certificate chain |
| certificates | UINT8[6000] | Ownership Service certificate chain |
| length_of_ocsp_response | UINT16[4] | Length of OCSP Response for each certificate in Ownership Service certificate chain |
| ocsp_response | UINT8[6000] | OCSP response for each certificate in the Ownership Service certificate chain signed by Intel® CAaaS OCSP Responder including the csme_nonce. The OCSP Responder certificate issued by the same CA as the certificate being checked for revocation. |
TEP_SET_TIME_CERTS_CMD Response
typedef struct
{
UPID_HECI_HEADER Header;
STATUS Status;
} TEP_SET_TIME_CERTS_CMD_Response;
| Field Name | Value | Description |
|---|---|---|
|
Header |
UPID_HECI_HEADER |
Response header |
|
Status |
STATUS |
TEP_STATUS values enum |
TEP_STATUS Values Returned:
| Status | Description |
|---|---|
|
TEP_SUCCESS |
All good |
|
TEP_INVALID_PARAMETER |
Intel® CSME failed to parse the input. |
|
TEP_INTERNAL_ERROR |
An internal CSME firmware error exception occurred |
|
TEP_BAD_SIGNATURE |
Certificate signature verification or OCSP response signature or certificate verification failed |
|
TEP_INVALID_CERT |
Certificate chain verification failed. |
|
TEP_TIME_NOT_SET |
Intel® CSME nonce returned in TEP_GET_TIME_SYNC_NONCE_CMD has expired (valid for 10 minutes) |
TEP_OWNERSHIP_VOUCHER_REQUEST_CMD
Sends Intel® CSME an ownership voucher request. This command is used for creating new ownership vouchers. To update an existing voucher, use TEP_OWNERSHIP_VOUCHER_UPDATE_REQUEST_CMD.
TEP_OWNERSHIP_VOUCHER_REQUEST_CMD Request
typedef struct
{
UPID_HECI_HEADER Header;
TEP_BINARY_VOUCHER_REQUEST binary_voucher_request;
} TEP_OWNERSHIP_VOUCHER_REQUEST_CMD_Request;
| Field Name | Value | Description |
|---|---|---|
| Header | UPID_HECI_HEADER | Request header |
| binary_voucher_request | TEP_BINARY_VOUCHER_REQUEST | The voucher request in binary format |
| Field Name | Value | Description |
|---|---|---|
| format | UPID_HECI_HEADER | 1 - for CMS JSON format |
| version | VERSION | First 2 bytes major number, second 2 bytes minor number |
| voucher_id | CHAR[36] | UUID ASCII |
| assertion | UINT32 | 0 - verified, 1 - vetted-claimed |
| owner_id | CHAR[36] | UUID ASCII |
| metadata | UINT8[256] | Binary coded in Base64. This data is opaque to Intel CSME |
| created_on_utc | UINT32 | UTC time in seconds - set by Intel CSME |
| expires_on_utc | UINT32 | UTC time in seconds |
| upid[64] | UINT8 | Intel Unique Platform ID - set by CSME |
| credential_type | UINT32 | 0 - domain CA certificate 1 - leaf certificate |
| hash_algo | UINT32 | 2 - SHA256 3 - SHA384 5 - SHA512 |
| owner_credential_hash | UINT8[64] | Hash of the owner credential hashed using hash_algo |
| ownership_expires_on_utc | UINT32 | UTC time in seconds |
| prev_voucher_id | CHAR[36] | UUID ASCII The voucher id of the voucher that is being updated. Zero if this is new voucher. |
| features | UINT32[10] | List of features this voucher authorizes: 101 - Intel AMT 150 - reserved for OEM feature These values map to feature OIDs in the ownership voucher |
TEP_OWNERSHIP_VOUCHER_REQUEST_CMD Response
Returns a JSON Ownership Voucher signed by Intel® CSME.
typedef struct
{
UPID_HECI_HEADER Header;
STATUS Status;
UINT32 voucher_request_len;
UINT8[TEP_MAX_JSON_VOUCHER_REQUEST] voucher_request;
} TEP_OWNERSHIP_VOUCHER_REQUEST_CMD_Response;
| Field Name | Value | Description |
|---|---|---|
|
Header |
Response header |
|
|
Status |
UINT32 | TEP_STATUS values enum |
| voucher_request_len | UINT32 | Size of the JSON voucher request |
| voucher_request | UINT8[TEP_MAX_JSON_VOUCHER_REQUEST] | CMS structure - CSME signed JSON voucher request |
CMS Structure Returned by Intel® TEP
| CMS Field | Value |
|---|---|
| contentType | signedData OID = 1.2.840.113549.1.7.2 |
| CMSVersion | 3 |
| digestAlgorithms | Message digest algorithm identifier: SHA-384 or SHA-512 |
| eContentType (in encapContentInfo) | Set to 2.16.840.1.113741.1.2.5.2. |
| eContent (in encapContentInfo) | the JSON voucher |
| certificates | Full CSME ODCA certificate chain for voucher signed by CSME FW. (Only Leaf Certificate for voucher signed by Ownership Service) |
| crls | Not included |
| signerInfo | Contains the signature and identifiers for finding the leaf certificate that signed the voucher, and additional signed attributes. |
| CMSVersion in signerInfo | 1 |
| signerIdentifier in signerInfo | IssuerAndSerialNumber is the "Issuer distinguished name" and "Certificate Serial Number" of the certificate that signed the voucher. |
| signedAttrs, a collection of attributes that are signed in signerInfo | content-type attribute (1.2.840.113549.1.9.3) equal to eContentType in encapContentInfo, message-digest attribute (1.2.840.113549.1.9.4) equal to digest of the encapContentInfo eContent being signed and signing-time attribute (1.2.840.113549.1.9.5). Intel® CSME uses digest algorithm SHA-384 |
| signatureAlgorithm in signerInfo | The algorithm to use for computing the signature over the message digest calculation. The algorithm used by Intel® CSME to sign a voucher request is ecdsa-with-SHA384 OID = 1.2.840.10045.4.3.3. The Ownership Service may use ecdsa-with-SHA384 or ecdsa-with-SHA512 OID = 1.2.840.10045.4.3.4 with a key on the secp-521r1 curve (RSA keys are not supported). |
| signature in signerInfo | The signature is over the digest of the complete DER encoded signerAttrs value contained in the signedAttrs field. The signedAttrs value contains the content-type and the message-digest attributes. |
SignerInfo ::= SEQUENCE {
version CMSVersion,
sid SignerIdentifier,
digestAlgorithm DigestAlgorithmIdentifier,
signedAttrs [0] IMPLICIT SignedAttributes OPTIONAL,
signatureAlgorithm SignatureAlgorithmIdentifier,
signature SignatureValue,
unsignedAttrs [1] IMPLICIT UnsignedAttributes OPTIONAL
}
TEP_STATUS Values Returned:
| Status | Description |
|---|---|
|
TEP_SUCCESS |
All good |
|
TEP_INVALID_PARAMETER |
Length in UPID_HECI_HEADER is not equal to the size of the request structure or one of the input parameters is not valid: format/version/feature value |
|
TEP_INTERNAL_ERROR |
An internal CSME firmware error exception occurred |
|
TEP_NOT_ALLOWED |
Certificate signature verification or OCSP response signature or certificate verification failed |
|
TEP_INVALID_CERT |
Certificate chain verification failed. |
|
TEP_TIME_NOT_SET |
Time and certificate chain were not set or 24 hours have passed since set. |
TEP_SET_OWNERSHIP_CMD
Sets the Ownership Voucher signed bythe Ownership Service into Intel CSME firmware.
TEP_SET_OWNERSHIP_CMD Request
typedef struct
{
UPID_HECI_HEADER Header;
UINT8[20] voucher_id;
UINT32 voucher_len;
UINT8[TEP_MAX_JSON_VOUCHER_REQUEST] json_voucher;
} TEP_SET_OWNERSHIP_CMD_Request;
| Field Name | Value | Description |
|---|---|---|
| Header | UPID_HECI_HEADER | Request header |
| voucher_id | CHAR[36] | Used by Intel® CSME firmware to look up the voucher request |
| voucher_len | UINT32 | The size of the JSON voucher request |
| json_voucher | UINT8[TEP_MAX_JSON_VOUCHER_REQUEST] | CMS structure - Ownership Service signed JSON voucher request |
TEP_SET_OWNERSHIP_CMD Response
typedef struct
{
UPID_HECI_HEADER Header;
STATUS Status;
} TEP_SET_TIME_CERTS_CMD_Response;
| Field Name | Value | Description |
|---|---|---|
|
Header |
UPID_HECI_HEADER |
Response header |
|
Status |
UINT32 |
TEP_STATUS values enum |
TEP_STATUS Values Returned:
| Status | Description |
|---|---|
|
TEP_SUCCESS |
All good |
|
TEP_INVALID_PARAMETER |
Length in UPID_HECI_HEADER is not equal to the size of the request structure or invalid input value for: version, voucher_id, prev_voucher_id, assertion, credential_type, hash_algo, features etc. |
|
TEP_INTERNAL_ERROR |
Unknown internal firmware exception |
|
TEP_NOT_ALLOWED |
Time and certificates must be set or refreshed |
|
TEP_INVALID_CMS |
The CMS structure has an invalid format or eContentType does not match 2.16.840.1.113741.1.2.5.2 |
TEP_GET_VOUCHERS_CMD
Returns list of voucher IDs. For Panther Lake: 1
TEP_GET_VOUCHERS_CMD Request
typedef struct
{
UPID_HECI_HEADER Header;
} TEP_GET_VOUCHERS_CMD _Request;
| Field Name | Value | Description |
|---|---|---|
| Header | UPID_HECI_HEADER | Request header |
TEP_GET_VOUCHERS_CMD Response
typedef struct
{
UPID_HECI_HEADER Header;
STATUS Status;
UINT32 num_vouchers;
CHAR[36][TEP_MAX_VOUCHERS] vouchers;
} TEP_GET_VOUCHERS_CMD_Response;
| Field Name | Value | Description |
|---|---|---|
|
Header |
UPID_HECI_HEADER |
Response header |
|
Status |
UINT32 |
TEP_STATUS values enum |
| num_vouchers | UINT32 | Number of vouchers in "vouchers" |
| vouchers | CHAR[36][TEP_MAX_VOUCHERS] | An array of voucher IDs of type CHAR[36] |
TEP_STATUS Values Returned:
| Status | Description |
|---|---|
|
TEP_SUCCESS |
All good |
|
TEP_INVALID_PARAMETER |
Length in UPID_HECI_HEADER is not equal to 0 |
|
TEP_INTERNAL_ERROR |
Unknown internal error |
TEP_GET_OWNERSHIP_STATE_CMD
Returns the ownership state for a specified voucher_id. Typically executed for finding the initial state, and after performing a Set command.
TEP_GET_OWNERSHIP_STATE_CMD Request:
typedef struct
{
UPID_HECI_HEADER Header;
UINT8[20] req_id;
CHAR[36] voucher_id;
} TEP_GET_OWNERSHIP_STATE_CMD_Request;
| Field Name | Value | Description |
|---|---|---|
| Header | UPID_HECI_HEADER | Request header |
| req_id | UINT8[20] | Random request id allocated by server to protect freshness |
| voucher_id | CHAR[36] | Voucher ID the state is requested for |
TEP_GET_OWNERSHIP_STATE_CMD Response
typedef struct
{
UPID_HECI_HEADER Header;
STATUS Status;
UINT8[20] req_id;
TEP_OWNERSHIP_CONTEXT voucher_context;
CSME_SIGNATURE signature
} TEP_GET_OWNERSHIP_STATE_CMD_Response;
| Field Name | Value | Description |
|---|---|---|
|
Header |
UPID_HECI_HEADER |
Response header |
|
Status |
UINT32 |
TEP_STATUS values enum |
| req_id | UINT8[20] | Random request id allocated by server to protect freshness |
| voucher_context | TEP_OWNERSHIP_CONTEXT | The owner context that holds the voucher and additional info about voucher issuer for voucher matching the requested voucher_id |
| signature | CSME_SIGNATURE | CSME signature on: status + req_id + voucher_context + CSME_SIGNATURE.timestamp + CSME_SIGNATURE. signature_mechanism |
TEP_OWNERSHIP_CONTEXT
| Field | Parameter Type | Description |
|---|---|---|
| ownership_status | UINT32 | 1 - REQUESTED, 2 - ACTIVE, 3 - EXPIRED, 4 - SUSPENDED |
| ownership_active_timestamp | UINT32 | The timestamp in UTC showing when the voucher became active |
| voucher_id | CHAR[36] | Voucher ID that the state is requested for. UUID ASCII |
| assertion | UINT32 | 0 - verified, 1 - vetted-claimed |
| owner_id | CHAR[36] | UUID ASCII |
| metadata | UINT8[256] | Binary coded in Base64. This data is opaque to Intel CSME |
| created_on_utc | UINT32 | UTC time in seconds - set by Intel CSME |
| expires_on_utc | UINT32 | UTC time in seconds |
| credential_type | UINT32 | 0 - domain CA certificate 1 - leaf certificate |
| hash_algo | UINT32 | 2 - SHA256 3 - SHA384 5 - SHA512 |
| owner_credential_hash | UINT8[64] | Hash of owner credential hashed using hash_algo |
| ownership_expires_on_utc | UINT32 | UTC time in seconds |
| prev_voucher_id | CHAR[36] | UUID ASCII The voucher id of the voucher that is being updated. Zero if this is a new voucher. |
| features | UINT32[10] | List of features this voucher authorizes: 101 - Intel AMT 150 - reserved for OEM feature These values map to feature OIDs in the ownership voucher |
| issuer_subject_dn | UINT8[256] | The issuer name in the certificate that signed the voucher |
| cert_serial_number | UINT8[20] | The serial number of the certificate that signed the voucher |
| cert_subject_dn | UINT8[256] | The subject name in the certificate that signed the voucher |
| X520_org_name | UINT8[64] | “X520OrganizationName attribute” (OID = 2.5.4.10) in the subjectAltName of certificate that signed the voucher |
| cert_policies | TPP_OID[10] |
Array of certificate policies OIDs in the certificate policies extension of certificate that signed the voucher. See the table Certificate Policy OIDs |
| OEM_ID | UINT16 | OEM_ID in voucher signing certificate |
CSME_SIGNATURE
| Parameter Name | Parameter Type | Description |
|---|---|---|
| time_stamp | UINT32 | UTC time when data was signed. Included in the signature |
| signature_mechanism |
UINT32 |
Intel CSME enum Included in the signature. Always ECDSA384 for Panther Lake. |
| signature | UINT8[512] | Actual signature length determined by Signature Mechanism |
| length_of_certificates | UINT16[7] | Length of each certificate in the chain, starting with the leaf certificate |
| certificates | UINT8[6000] | The certificate chain, certificates concatenated one after another, starting with the leaf certificate |
TEP_STATUS Values Returned
| Status | Description |
|---|---|
| TEP_SUCCESS | All good |
| TEP_INVALID_PARAMETER | Length in UPID_HECI_HEADER is not equal to the size of the request structure invalid voucher_id |
| TEP_INTERNAL_ERROR | Unknown internal firmware exception |
TEP_OWNERSHIP_VOUCHER_UPDATE_REQUEST_CMD
Allows updating the "ownership-expires-on" and "credential-hash" of an existing voucher. Can be used to reactivate an expired voucher or to expire a voucher to enable deleting it (by giving the voucher an expiry date that has passed).
TEP_OWNERSHIP_VOUCHER_UPDATE_REQUEST_CMD Request
typedef struct
{
UPID_HECI_HEADER Header;
binary_voucher_request TEP_BINARY_VOUCHER_REQUEST;
} TEP_OWNERSHIP_VOUCHER_UPDATE_REQUEST_CMD_Request;
| Field Name | Value | Description |
|---|---|---|
| Header | UPID_HECI_HEADER | Header that identifies the command |
| binary_voucher_request | TEP_BINARY_VOUCHER_REQUEST | The voucher request in binary format |
TEP_OWNERSHIP_VOUCHER_UPDATE_REQUEST_CMD Response
typedef struct
{
UPID_HECI_HEADER Header;
STATUS Status;
UINT32 voucher_request_len;
UINT8[TEP_MAX_JSON_VOUCHER_REQUEST] voucher_request;
} TEP_OWNERSHIP_VOUCHER_UPDATE_REQUEST_CMD_Response;
| Field Name | Value | Description |
|---|---|---|
|
Header |
Header that identifies the command | |
|
Status |
UINT32 |
TEP_STATUS values enum |
| voucher_request_len | UINT32 | Size of the JSON voucher request |
| voucher_request | CHAR[36][TEP_MAX_VOUCHERS] | CMS structure - Intel CSME signed JSON voucher request |
TEP_STATUS Values Returned
| Status | Description |
|---|---|
|
TEP_SUCCESS |
All good |
|
TEP_INVALID_PARAMETER |
Length in UPID_HECI_HEADER is not equal to the size of the request structure or invalid field in the voucher request |
|
TEP_INTERNAL_ERROR |
Unknown internal firmware exception |
|
TEP_NOT_ALLOWED |
No time or certificate chain set or certificates validity expired |
TEP_OWNERSHIP_REMOVE_CMD
Removes a voucher.
TEP_OWNERSHIP_REMOVE_CMD Request
typedef struct
{
UPID_HECI_HEADER Header;
CHAR[36] voucher_id;
} TEP_OWNERSHIP_REMOVE_CMD_Request;
| Parameter Name | Parameter Type | Description |
|---|---|---|
| Header | UPID_HECI_HEADER | Header that identifies the command |
| voucher_id | CHAR[36] | Voucher ID to remove. UUID ASCII |
TEP_OWNERSHIP_VOUCHER_UPDATE_REQUEST_CMD Response
typedef struct
{
UPID_HECI_HEADER Header;
UINT32 status;
} TEP_OWNERSHIP_REMOVE_CMD_Response;
| Field Name | Value | Description |
|---|---|---|
|
Header |
UPID_HECI_HEADER |
Header that identifies the command |
|
Status |
UINT32 |
TEP_STATUS values enum |
TEP_STATUS Values Returned
| Status | Description |
|---|---|
| TEP_SUCCESS | All good |
| TEP_INVALID_PARAMETER | Length in UPID_HECI_HEADER is not equal to the size of the request structure |
| TEP_INTERNAL_ERROR |
Unknown internal firmware exception |
| TEP_INVALID_VOUCHER | Invalid voucher ID |
| TEP_NOT_ALLOWED | Invalid state – voucher not expired |
Use Cases
The following table describes main use cases for Intel UPID.
| Use case | To check whether supported, do the following: |
|---|---|
| Read the Intel UPID | Query the Intel MEI driver for the supported Intel MEI Client GUIDs and verify that the UPID GUID is returned. |
| Attest the Intel UPID |
Or
|
Use Case: Read the Intel UPID
To read the Intel UPID from the OS:
- Set the Intel UPID feature state to Enabled. This can be accomplished by one of the following methods:
- BIOS setting
- OS WMI Command (SetUniquePlatformIDFeatureState)
- Intel MEI command: Using the UPID_PLATFORM_ID_FEATURE_STATE_SET command.
2. Read the Intel UPID using the UPID_PLATFORM_ID_GET command.
3. Set the Intel UPID feature state to Disabled using one of the methods in Step 1.
Use Case: Attest the UPID
The following describes the high-level flow for Intel UPID attestation:
- Set the Intel UPID feature state to Enabled. This can be accomplished by one of the following methods:
- BIOS setting
- OS WMI Command (SetUniquePlatformIDFeatureState)
- Intel MEI command: Using the UPID_PLATFORM_ID_FEATURE_STATE_SET command.
- The attestor application sends a challenge request to the Intel CSME firmware via the Intel MEI UPID_OEM_PLATFORM_ID_SIGN command. The Intel CSME application uses its Intel UPID attestation key to sign the challenge and return a signed challenge response.
-
The attestor application obtains the Intel UPID IDevID certificate chain via the UPID_OEM_PLATFORM_ID_GET_CERTIFICATE_CHAIN command.
- The attestor application retrieves the leaf certificate from the first entry in the certificate chain and verifies that this is an Intel UPID attestation certificate by checking that the Extended Key Usage (EKU) field includes the OID 2.16.840.1.113741.1.2.4.6 (for BIOS Intel UPID attestation) or 2.16.840.1.113741.1.2.4.7(for OS Intel UPID attestation).
- If valid, the attestor verifies that this is a Production system Intel CSME certificate chain (and not an Engineering Sample or Debug system or other Intel chipset IP certificate). This is verified by the Issuer Field in the ROM ODCA certificate:
- Find the CSME ROM ODCA Certificate: This is the 4th certificate in the chain with the Subject Field Common Name attribute containing “ROM CA”.
- In the Issuer field, the organizationalUnitName Attribute (OU) must have a prefix equal to either ODCA 2 CSME P or On Die CSME P, where P stands for Production.
- If valid, the attestor application retrieves the public key from the leaf certificate and verifies the challenge response signature. See Verifying the Challenge Response Signature.
- If the challenge response is valid, the attestor verifies the certificate chain up to the Intel iKGF Root CA installed in the service (https://tsci.intel.com/content/OnDieCA/certs/OnDie_CA_RootCA_Certificate.cer), and verifies that no certificate in this chain has been revoked by the iKGF CA CRL.
- If the certificate chain is valid, the attestor application verifies the Intel UPID against the IDevID certificate chain:
- Retrieves the OEM Platform ID from the 520SerialNumber attribute in the Subject field of the IDevID certificate, and verifies it against the first 32 bytes of the Intel UPID.
- Retrieves the hwSerialNum in the SubjectAltName field in the certificate and compares it with the second 32 bytes of the Intel UPID.
- If valid, the attestor application verifies that the first 20 bytes of the hwSerialNum in the SubjectAltName field match the first 20 bytes of the SHA256 hash of the ROM ODCA Certificate (identified in Step 4).

Verifying the Challenge Response Signature
- Decrypt the signature field returned in the challenge response with the public key that resides within the Intel UPID IDevID leaf certificate per the SignatureMechanism parameter in the response.
- Compute the hash of the challenge data in the dataToSign parameter that was sent to CSME FW in UPID_OEM_PLATFORM_ID_SIGN Intel MEI command, per the hash function in SignatureMechanism.
- Compare the decrypt signature field in Step 1 with the hash value in Step 2. Both values should be equal.
Verification Method
Any open-source crypto library that verifies ECDSA signatures can be used for verifying the challenge response signature returned from the Intel CSME firmware.
For example, the Open SSL ECDSA_verify function can be used with the following input parameters:
Method declaration:
int ECDSA_do_verify(const unsigned char *dgst, int dgst_len,
const ECDSA_SIG *sig, EC_KEY* eckey);
Method call:
ret = ECDSA_do_verify(digest, 48, sig, eckey);
|
Parameter |
Meaning |
|
Digest |
Hash of the dataToSign |
|
Sig |
The returned signature field in the challenge response transformed to ECDSA_SIG encoding |
|
eckey |
The public key that resides in the IDevID (leaf) certificate returned within the challenge response. Intel® ME eckey curve type is nist p384 |
Verifying the OCDA Certificate Chain
To verify the ODCA certificate chain, the user application is required to check all signatures in the chain and check that the root certificate matches the iKGF root certificate. This can be accomplished by the standard PKI certificate chain verification method, taking the root CA from a trusted Intel site.
If attestation fails due to a signation certification verification error, the Intel UPID certificate should not be trusted.
Intel UPID WMI Provider Commands
WMI is a Windows management subsystem that allows an administrator to access Intel MEI APIs using a standard interface.
Notes:
1. Before you can use WMI commands, you need to ensure that WMI is supported on the system that you are querying.
To determine whether your computer has the Intel CSME WMI provider (which is usually pushed by Microsoft Windows Update), perform one of the following actions:
• Run a WMI command and check whether it succeeds.
• Open a Command window and run sc query. Check whether the Intel(R) Management Engine WMI Provider Registration service is listed.
• Open a PowerShell window and run the Get-Service command. Check whether the Intel(R) Management Engine WMI Provider Registration is listed. This can also be found in the device manager (Software components \ Intel(R) Management Engine WMI Provider).
If your computer is missing the Intel CSME WMI provider, you need to install the Intel CSME Software package, which includes the provider.
The Intel CSME Software package and installation instructions are available from your OEM.
Alternatively, you can download the Intel CSME Software from Intel’s Download Center. See the section Installing Intel® CSME Software Components in the
Intel® Converged Security and Management Engine Software Installation and Configuration Guide included with the software package.
2. The WMI commands must be executed with OS Admin control.
Set Intel UPID Feature State via WMI
To enable the feature state via WMI, open PowerShell and execute:
Invoke-CimMethod -Namespace "root\Intel_ME" -ClassName ME_System -MethodName setUniquePlatformIDFeatureState -Arguments @{ state = $True}

Get Intel UPID Feature State via WMI
To retrieve the feature state, open PowerShell and execute:
Invoke-CimMethod -Namespace "root\Intel_ME" -ClassName ME_System -MethodName getUniquePlatformIDFeatureState
Read Intel UPID via WMI
Note: This command is available only when the Intel UPID state has been set to Enabled via the BIOS, WMI or an Intel MEI command.
To read the Intel UPID, open PowerShell and execute:
Invoke-CimMethod -Namespace "root\Intel_ME" -ClassName ME_System -MethodName getUniquePlatformID
The system’s unique identity is displayed in two parts:
- Intel CSME Platform ID
- OEM platform ID. If the ID has not yet been set, this field will be filled with zeros.