Virtualization is important to cloud workloads. It's the invisible fence in the server that lets different software processes peacefully coexist. It's what has allowed cloud computing to explode in popularity and allowed much more efficient use of compute resources. Over the years, virtualization has evolved with better security, increased efficiency, and more performance. As existing virtualization solutions evolved and matured, the code bases grew to continue supporting an increasing number of new technologies while supporting legacy devices. With the explosion in popularity of running different sets of workloads in the cloud, the need to support older legacy hardware has waned. The time has come for a new solution that is purpose built for efficiently running those cloud workloads with security as a primary focus. This is what inspired Intel to start the Cloud Hypervisor project to run these modern cloud workloads.
The existing solutions in the market have been great for many years. Many types of operating systems and workloads can be run. You can even emulate a floppy drive from the 1990s. But, as any software code base grows larger, it greatly increases the chances of a malicious actor compromising it. To see examples, look at the sheer number of security vulnerabilities that are ongoing for any operating system. Intel initiated the Cloud Hypervisor project to start from a small code base without the old legacy support. Starting a new project allows rapid innovation of new features. It allows these modern cloud workloads to achieve high performance running isolated from other workloads all while enhancing security.
What Is Cloud Hypervisor?
Fundamentally, Cloud Hypervisor is a virtual machine monitor (VMM) that can interface with a hypervisor to launch and manage virtual machines (VM). It offers services to VM guests including virtualized or paravirtualized devices. The VMM tracks everything that happens in a VM and is responsible for monitoring and enforcing policies. The hypervisor it interfaces with is the Linux* kernel-based virtual machine (KVM), which is responsible for providing the interface between the VM and the host system. The words VMM and hypervisor are often used interchangeably, but together they allow the creation, launch, and management of virtual machines on top of an existing operating system.
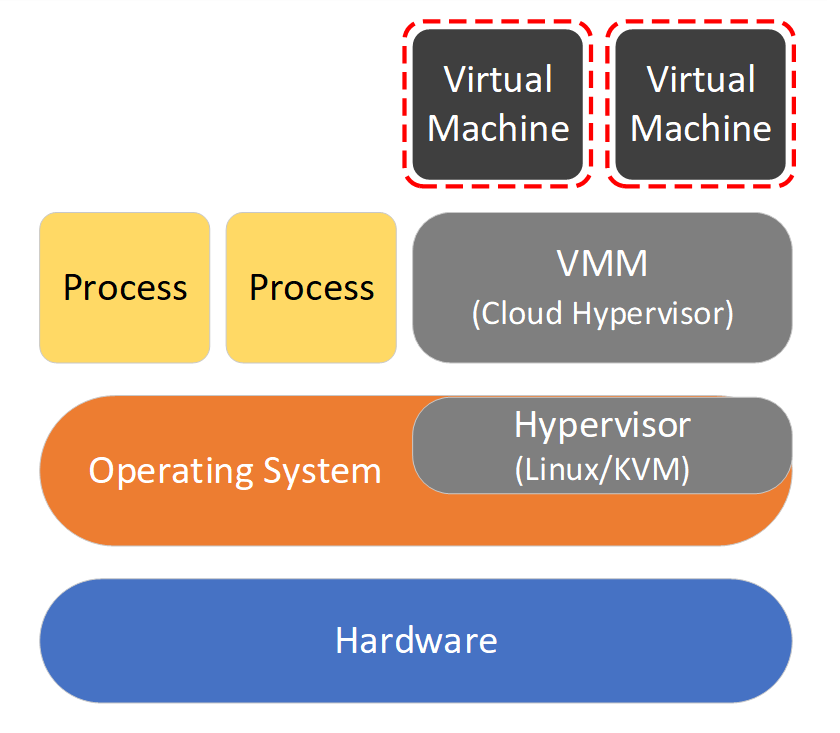
Figure 1: Cloud Hypervisor VMM
Hosted by the Linux Foundation*
The Cloud Hypervisor project isn't just an Intel project now. Intel seeded the initial code and worked alongside Alibaba*, Arm*, ByteDance*, and Microsoft* to cofound this as an officially hosted project from the Linux Foundation*. This type of guidance and open governance is key to having Cloud Hypervisor adopted and supported industry wide. It doesn't just benefit Intel. It benefits everyone in the industry so that these new cloud workloads are more efficient, more performant, and more secure across multiple architectures. Intel is active in the project with maintainers on the architecture committee helping to drive the specifications, bug fixes, and new features. This ensures that cloud workloads take advantage of all the unique optimizations that Intel® processors and accelerators provide for a smooth, stable, and secure experience.
Cloud Hypervisor Features
So, what makes Cloud Hypervisor unique? For example, the same support for legacy hardware is no longer needed for cloud workloads, which helps to reduce the code base and the attack surface area. Every API call, function, and stacked array is another opportunity that could be exploited. A smaller code base means less opportunity for these security escapes. Many older hardware devices were architected without a security-first mindset. When those devices are emulated, the same vulnerabilities can perpetuate into the VMMs. In fact, some of the worst security escapes have been from legacy devices like this floppy disk controller. Cloud Hypervisor eliminates this problem from the start. A smaller code base also means it is easier to audit the code.
Another important security feature of Cloud Hypervisor is that it is written in the Rust* programming language. The Rust programming language by nature has strong memory protection built in. Unsafe keywords must be used to explicitly opt out of this memory protection. Many Common Vulnerabilities and Exposures (CVE) that get reported are due to memory safety issues. The Rust programming language statically enforces many properties beyond just memory safety. This includes ensuring that null pointers are safe, checking for unitialized arrays, and protecting against buffer overflows. Unsynchronized access of memory from multiple threads isn't allowed by default. The Rust programming language also performs well, which is why it is well suited for a VMM like Cloud Hypervisor.
Cloud Hypervisor also supports many features that you would expect in a VMM.
- Support for Linux and Windows* guests
- Multiple architectures (x86-64 and Aarch64)
- Snapshot, restore, and live migration
- Non-uniform memory access (NUMA) topologies for better workload placement across CPUs and memory controllers
- Hot plug of CPU, memory, and devices using ACPI
- Nested guests using Intel® Virtualization Technology (Intel® VT) for Directed I/O (Intel® VT-d) for direct memory access (DMA) protection.
- Sandboxing with seccomp for enhanced security
- Advanced guest memory management using virtio-mem and virtio-balloon
- HTTP REST API that allows programmatic control of the VMM by cloud orchestration and cloud native technologies such as Kata Containers*
Enhanced Security with Intel® SGX and Intel® TDX
Intel has added initial support for Intel® Software Guard Extensions (Intel® SGX) so that software running inside a Cloud Hypervisor VM can access encrypted memory enclaves. Guest operating systems can attest and create Intel SGX enclaves just the same as software running bare metal. Imagine a service mesh running inside a Cloud Hypervisor VM that uses Intel SGX to run the signing of a public key inside this encrypted memory. It's layers upon layers of security to provide protection to a private key from other software processes and even the host itself.
As the industry moves to confidential computing, Intel has added support for the Intel® Trust Domain Extensions (Intel® TDX). This is a set of architectural elements designed to deploy hardware-isolated virtual machines called trust domains. It integrates technologies like Multi-Key Total Memory encryption (MKTME) that enables a VMM like Cloud Hypervisor to separately encrypt VMs with unique encryption keys owned by tenants. It also includes remote attestation and virtual machine extensions (VMX). The intersection of Cloud Hypervisor, Intel TDX, and Kata Containers allows unmodified container workloads to isolate sensitive data not just from other workloads but from the host itself. In a cloud native environment, where Kubernetes works with Kata Containers and Cloud Hypervisor, when a pod is created, Cloud Hypervisor allocates and attests an encrypted enclave in memory and boots a VM within that enclave. Kata Containers downloads a container image through an encrypted connection, unpacks the image, and manages the lifecycle of the workload. This is the next generation of trust for cloud workloads that is made possible with Cloud Hypervisor and Intel TDX.
Ready for Evaluation
Cloud Hypervisor is an exciting new project with broad support from key industry players. Now that it is governed by the Linux Foundation, it is ready to be evaluated across a broad set of cloud workloads. Try it at GitHub* and let the team know what you think. Cloud Hypervisor aims to be the ideal choice for all cloud workloads.